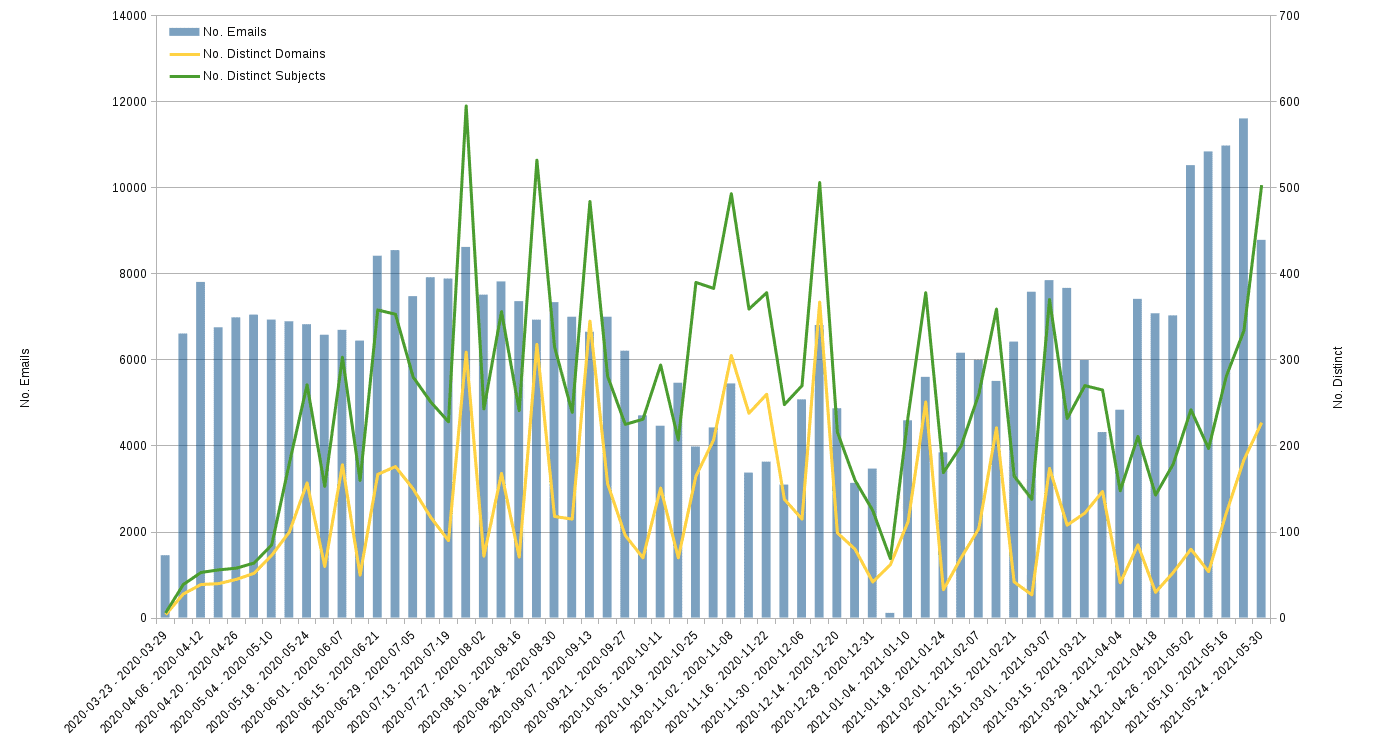
Overview
- Time period: March 2020 – May 28, 2021
- Number of emails sent: >405,000
- Subject lines used: 5,881
- Mailboxes targeted: 2,099
- Sender domains used: 821
Tessian’s Research & Intelligence team have identified a pattern of suspicious email activity across the Tessian platform, originating from a US-based online “leader in legal education”. The first email campaigns were detected in early 2020. In every campaign, the organization appears to be promoting discounts on educational courses or new curriculum. New domains – our team has observed 2-3 new domains appearing per week – were used to evade spam filters and SEGs.
Who was targeted?
Over 10% of our customer base received one of the campaigns from this legal education firm. 65% of the targeted customers are in the Legal sector; 25% are in Financial Services. Almost all targeted customers are US-based.
Nearly every customer has a legacy Secure Email Gateway (SEG) and Tessian Defender as part of their inbound email tech stack. These emails bypassed the SEGs, but were flagged as potentially malicious by Tessian Defender.
One single law firm received an astounding 280,000 emails from this organization in a little over a year. Other Tessian customers received several hundred to thousands in the same time frame. Normally high-volume campaigns like this are not very targeted or customized to the recipient. In this case, the sender has taken a scatter-shot approach with the hope that a fraction of the recipients engage. Even if these emails are not malicious, they are certainly a nuisance – especially for busy attorneys.
What was the angle?
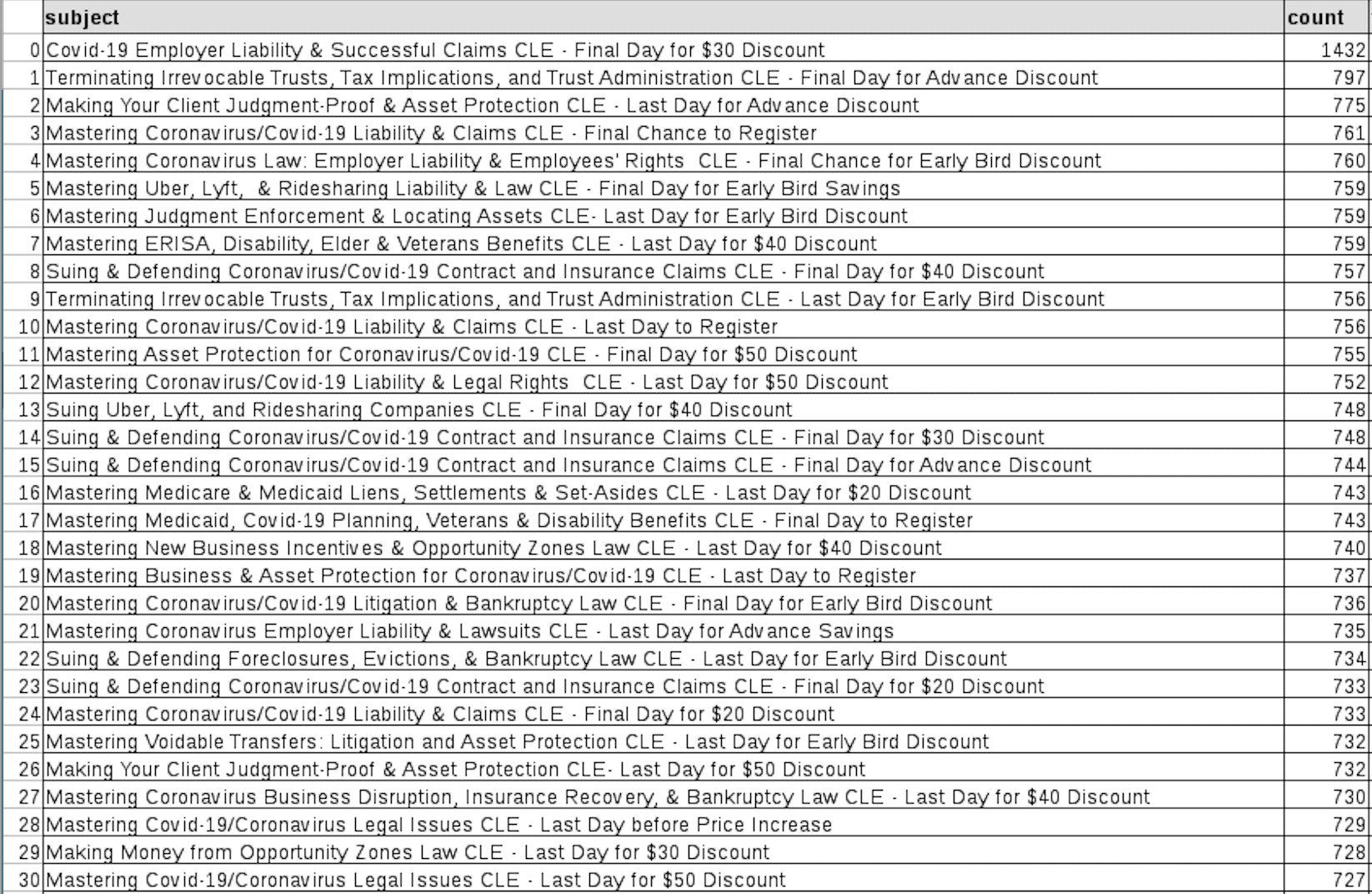
Nearly 6,000 subject lines were used in these email campaigns. Notable themes and keywords include:
- Coronavirus / COVID-19
- Cryptocurrency, Blockchain, Bitcoin and Smart Contracts
- AirBnB & Short-Term Rental Law
- Marijuana, Hemp and Cannabis Law
- Judgments & Asset Protection
- Uber, Lyft & Ridesharing law
- Discounts
- Last/final day to register
It appears that they are attempting to capitalize on new or trending legal topics, which could be particularly relevant to law firms and financial services institutions.
Suspicious, not necessarily malicious
While this legal education provider may be a legitimate organization, their website is insecure (no SSL certification, no padlock icon), and more importantly, the way they are building and distributing these email campaigns is suspicious; their tactics mimic those deployed by cybercriminals to evade defenses. For example, the emails are often sent from a recently registered domain by a sender the recipient will probably not have seen before. These are two key indicators that trigger Tessian Defender.
In a little over a year, the legal education provider registered over 800 domains; sent emails from over 825 email addresses; and used about 20 different display names. This sort of behavior indicates that they were deliberately crafting emails to bypass rule-based filtering. [Read more about display name and domain manipulation.]
Why? Once a domain has developed a reputation for spam, then it can be added to a spamming blacklist, which will be a significant factor considered by spam filters. Registering a new domain with a fresh or unknown reputation is the easiest way to get around this. This is not dissimilar to how hackers create phishing attacks.
The emails often also contained a sense of urgency to bait the recipient into buying or signing up to something while a certain discount is still available. Urgency (i.e. “Last day to register”) is another technique regularly employed in phishing emails. Most of the URLs in the emails pointed to a legitimate website called Constant Contact (an email marketing tool).
What can you do about it?
General guidance
- Limit how far you share your email address across the internet. Keep it private unless it is essential to share it.
- Do not click on any links in spam emails as they could be malicious.
- Mark it as spam or move it to your spam/junk email folder to help train the spam recognition algorithm. After marking it as spam, delete the email from your spam/junk folder.
If you’re a Tessian customer
- Review attacks in the Tessian portal and add senders to a denylist to be blocked before reaching inboxes in the future.
- Review attacks in the Tessian portal and remove emails from employee inboxes.
- Use the Human Layer Risk Hub to understand which employees are most at risk of phishing; then notify them individually or create customized warnings to educate them about the risk.
The primary way for avoiding spam is to limit how much you share your email address across the internet. Be cautious of who and what services you sign up to with your email address – whether it’s your personal or business email address. Some services may willingly sell your information to spammers or marketers. The key difference between marketing emails and spam is that marketing emails should only be sent to emails that have consented to receive them. To comply with regulations like GDPR and CCPA, marketing emails must also provide an easy way to opt out of future emails, for example, by including an unsubscribe link or button in the email.
Last but not least, if you’re a lawyer, always make sure the provider and courses of legal training are accredited.
Charles Brook
Threat Intelligence Specialist