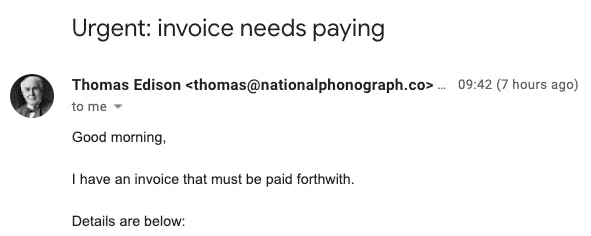
Jargon is a hallmark of all industries. Cybersecurity is no different, but using the right security terminology has a real impact. When an organization’s data and systems are threatened by spear phishing attacks, being aware of evolving trends and the definitions of key terms could be the difference that helps prevent the next threat.
Spear phishing is the number one threat facing businesses today, but research still suggests that “lack of knowledge and awareness about cyber-attacks could hinder the growth of the spear phishing protection market.”
In this article we define and explain key spear phishing concepts and terms. (To learn more about how to prevent spear phishing attacks with machine-intelligent technology, read about Tessian Defender.)
Spear phishing definition, and other attack types
Although media outlets and security companies rightly pay a lot of attention to spear phishing, advanced impersonation spear phishing attacks come in many forms. Once you’ve read our breakdown of different key terms and what they mean, you’ll come away with a clearer understanding of the range of sophisticated inbound email threats.
Spear phishing
Spear phishing describes an advanced impersonation phishing attack directed at specific individuals or companies. (Head to the “Other useful terms” section below to see a definition of regular “bulk” phishing.) Similar to “bulk” phishing, spear phishing attacks are designed to trick people into taking an action like transferring funds or clicking on a malicious link. In contrast to bulk phishing, spear phishing attackers often gather and use personal information about their target to increase their probability of success. Because spear phishing emails are low-volume as well as more sophisticated in their construction and convincing in execution, they are far harder for traditional email security products to catch.
CEO fraud / executive fraud
CEO fraud is a type of spear phishing attack where attackers impersonate a CEO or another high-level executive. Here, attackers aim to trick the executive’s colleagues into carrying out actions that place data, money and/or credentials at risk. Attackers often use social engineering techniques (see “Other useful terms” below) to convey urgency and prevent targeted employees from thinking twice about following the instructions of the “CEO”. A notorious example of this kind of fraud saw an impersonation of Pathé France’s CEO lose Pathé €19.2m.
Whaling
Whaling is related to CEO fraud, with a key difference: instead of impersonating senior executives and targeting lower-ranking employees, attackers target the big fish themselves (hence the term). A whaling attack might involve attackers trying to get the executive in question to divulge key credential information or other sensitive organizational data. This information can then be used to access confidential systems, or to make subsequent spear phishing attacks within the organization more authentic and effective. Because they are many times more likely to be targeted than rank-and-file employees, because they tend to be very busy, and because of their access and influence, senior executives can be especially profitable targets for attackers.
Forms of impersonation used in spear phishing attacks
Although all spear phishing attacks revolve around impersonation of some kind, impersonation itself can take many forms. Attackers impersonate people on email in order to:
• Steal money, data and credentials
• Compromise systems
• Take over accounts
Essentially, all spear phishing attacks use impersonation as a strategy. Mechanisms differ from the easy (display name impersonation) to the complex (direct spoofing). Here’s how we break impersonations down:
Business Email Compromise
According to the FBI, Business Email Compromise (BEC) attacks cost organizations $1.2bn in 2018 alone. BEC is closely related to spear phishing – and commonly confused with it – but is potentially still more damaging and severe. Attackers impersonate employees or external counterparties and send spear phishing emails to people within the organization being targeted, using social engineering techniques to convince targets to wire funds outside the organization or to click on dangerous links that risk compromising systems and/or data.
Readers should bear in mind that there are several different interpretations of BEC. For example, it’s often confused with Account Takeover (ATO): ATO describes the unauthorized takeover of someone’s actual account, using harvested credentials or “brute force” hacking.
Domain impersonation
These attacks involve attackers spoofing or impersonating an organization’s domain in order to appear legitimate. There are three main kinds of domain impersonation: root, top-level and subdomain. Below is an example of each of these impersonations, using the domain companyinc.com as a starting point:
• Root: companyceo@companyinc-outbound.com OR companyceo@c0mpanyinc.com
• Top-level: companyceo@companyinc.net
• Subdomain: companyceo@companyinc.secured-email.com
Display name impersonation
Display name impersonations involve attackers setting deceptive display names on their email accounts in order to mislead recipients. This might mean impersonating a senior executive within a company, or the name of a key supplier or partner. The technical skill required is effectively zero: most mainstream email clients offer users ways to change display names in their account settings. Display name impersonations are particularly effective when received on mobile devices, as the sender’s actual email address is usually hidden.