Solution Briefs
An Essential Layer of Inbound Email Security For Financial Services
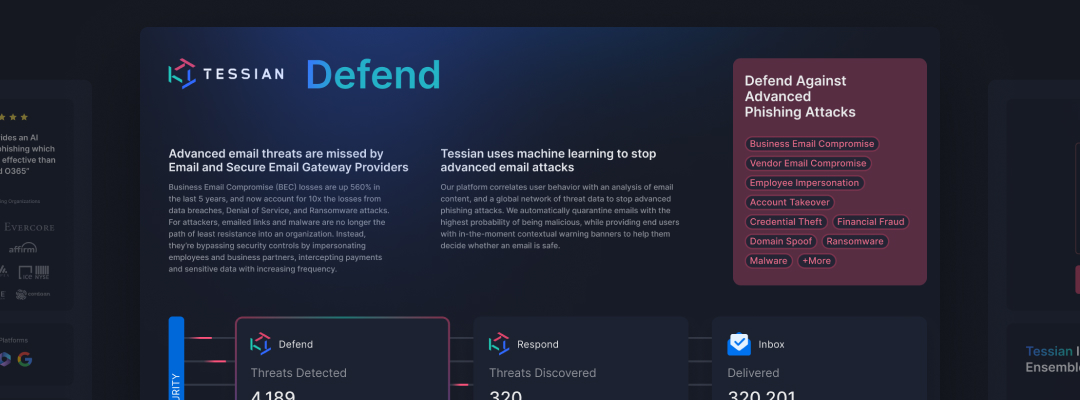
Tessian Defender is an essential layer of inbound email security for financial institutions, and helps some of the world’s most respected organizations prevent the advanced inbound threats, including spear phishing, business email compromise (BEC), account takeover (ATO), and CEO Fraud.
Download the solutions brief to learn…
- Why inbound threats are top of mind for security leaders in financial services
- How Tessian detects and prevents threats that slip past O365, Outlook, and other native tools and legacy solutions
- How Tessian’s in-the-moment warnings have helped Schroders, Prudential, Evercore, and more improve their security posture over time
- What security leaders at organizations like yours are saying about Tessian inbound email security