Stop Sensitive Data Loss Over Email
Stop the Full Spectrum of Email Risks
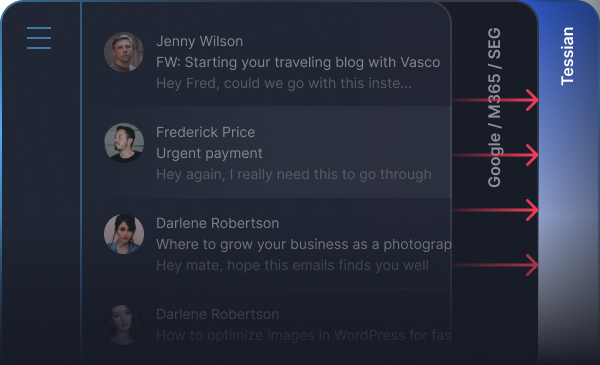
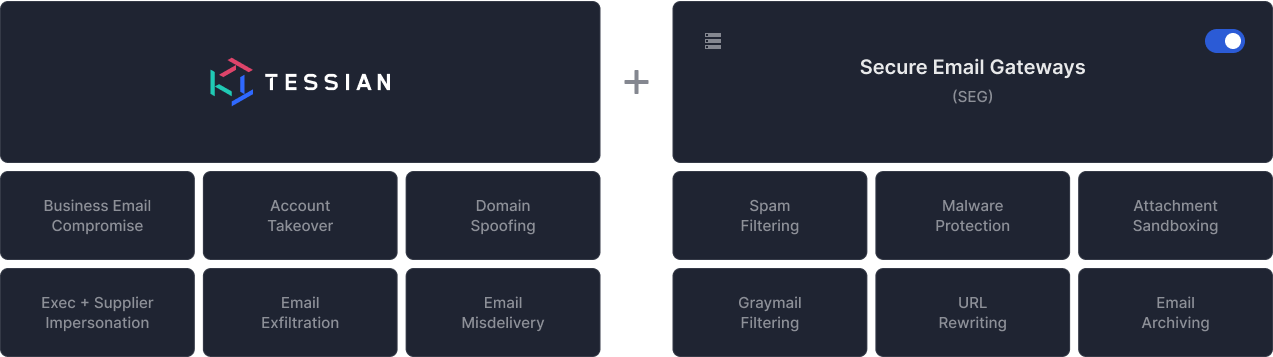
Without an AI based approach that leverages behavior and content analysis - sensitive data will continue to slip through general purpose DLP software and secure email gateways.
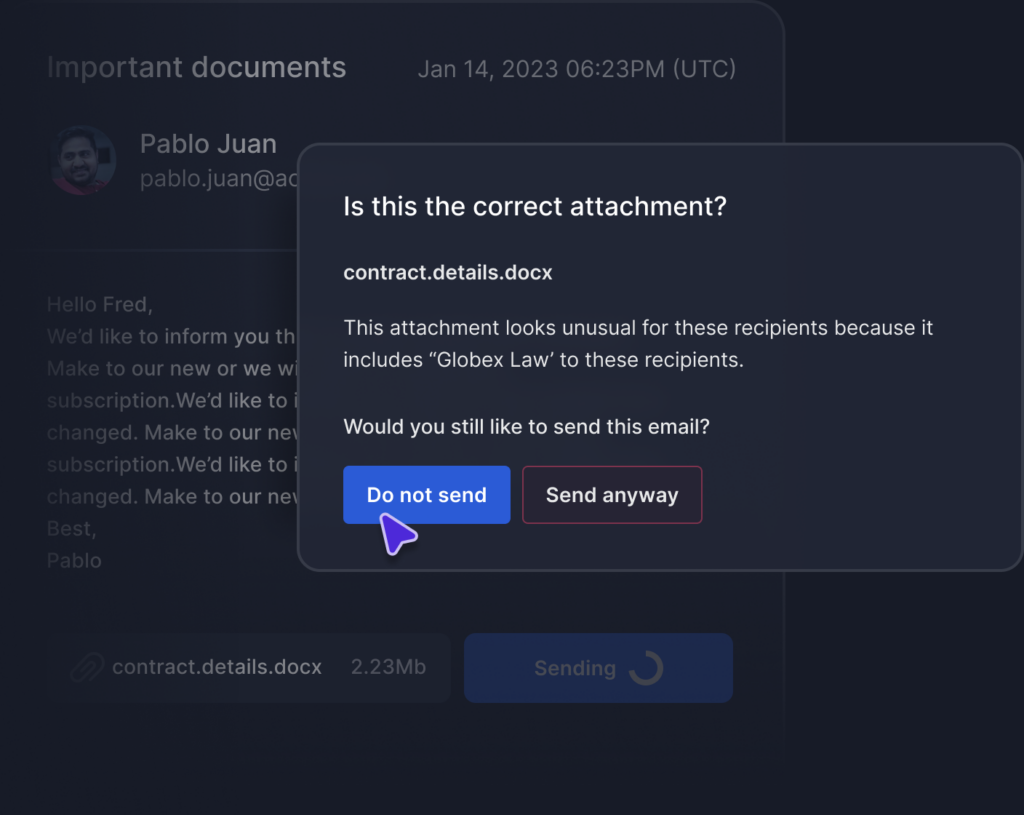
Tessian AI uses relationship graphs, deep content inspection and behavioral analysis to understand typical employee behavior. That means your organization’s sensitive data is protected when the wrong recipient is auto-filled, or employees share the wrong attachment.
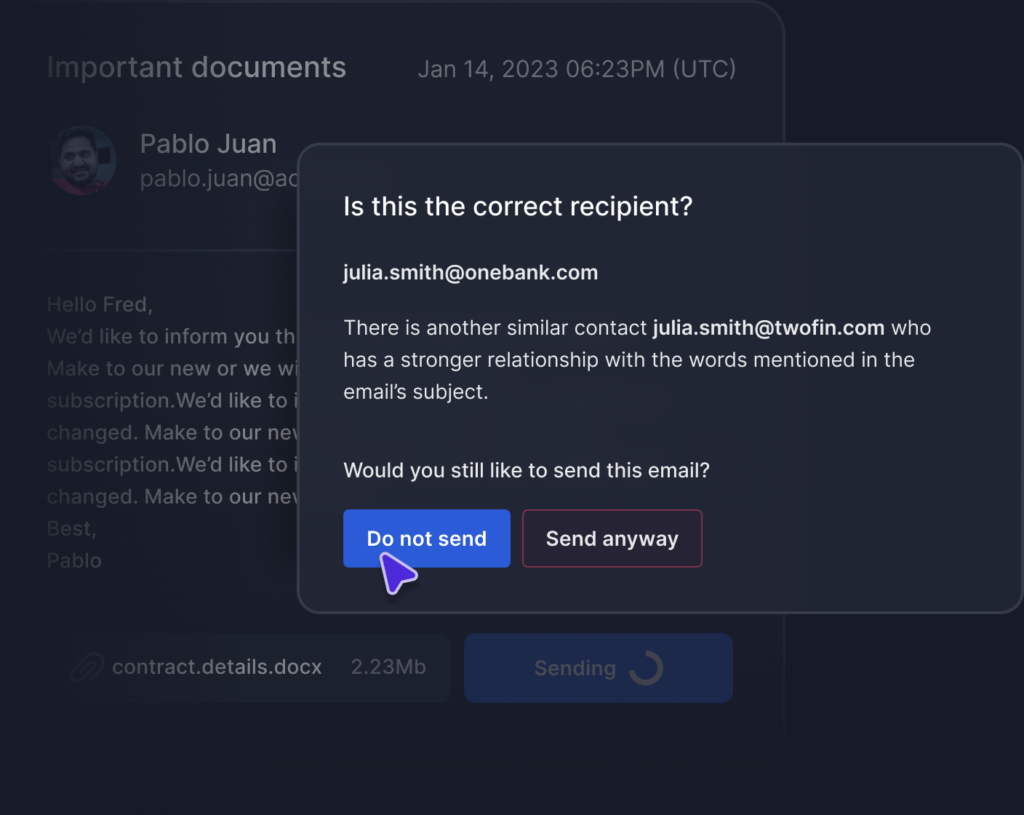
Tessian AI learns and maintains a robust understanding of employees’ normal behaviors by analyzing hundreds of data points on every email and its attachments.
Tessian detects and prevent data exfiltration incidents on emails before they’re sent, while providing in the moment coaching to improve security awareness.
Combine Tessian’s AI-based classifiers with DLP controls like Microsoft Information Protection to increase effectiveness. Our highly configurable, intelligent policy engine allows you to define data classification conditions using both AI-based and logic to meet industry standards and compliance requirements.
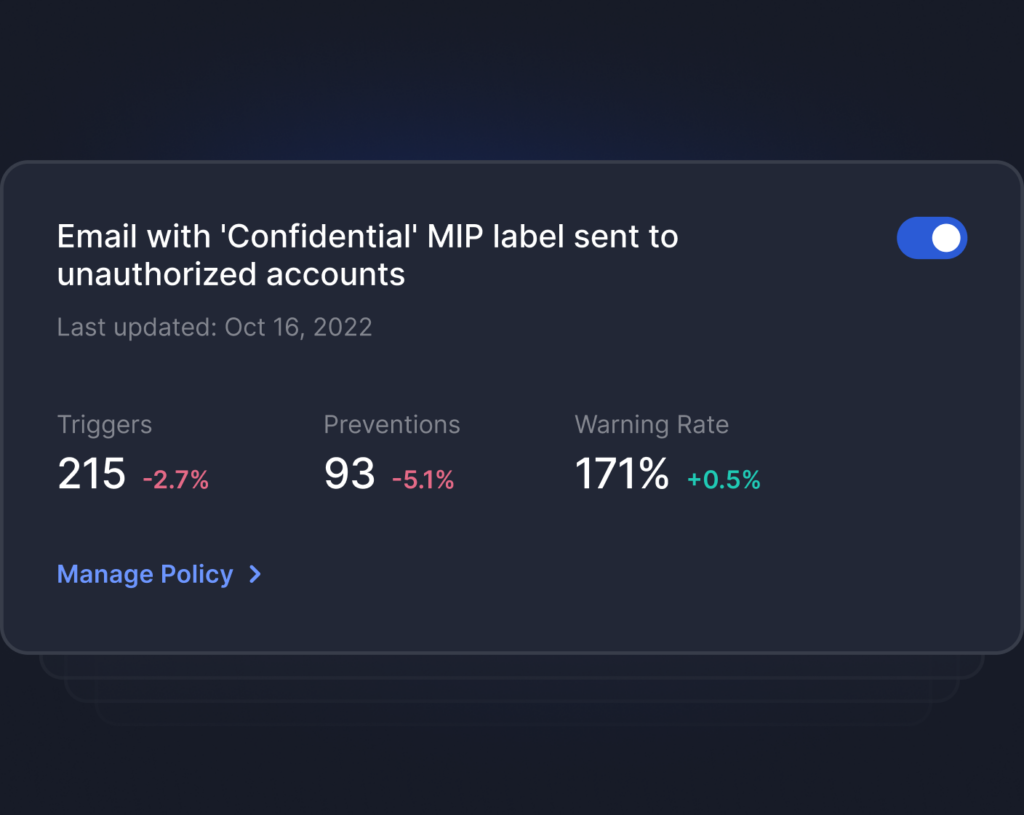
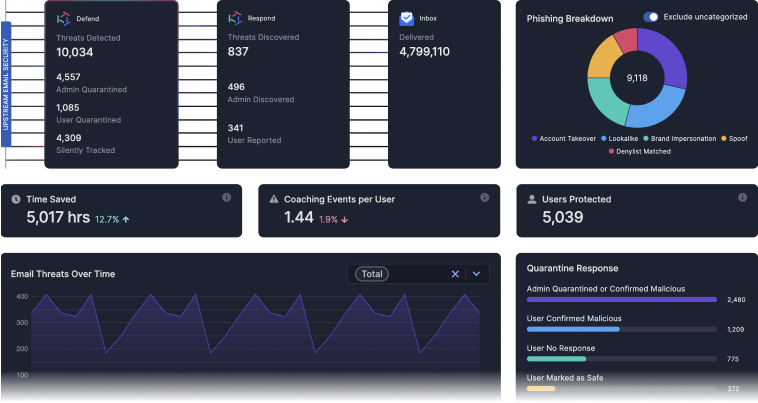
With Tessian, you can investigate detailed logs that include event type, details, user and IP address for all email based data loss events. Leverage automated reporting and intelligent insights on employee behavior on the Tessian Protect dashboard to easily quantify risk, track non-compliant activity and benchmark against peers.

See Tessian in Action
featured resources
-
Tessian’s Guide to Protecting Against Insider Risk on Email
Every day, inadvertent human mistakes and malicious behavior on email put organizations and their customers’ data at risk, breaching mandatory industry and data protection regulations. Download Tessian’s Guide to Protecting Against Insider Risk on Email to learn about why the ever evolving issue of data loss on email needs a new approach.Download the Guide -
Tessian Protect Data Sheet
Tessian’s behavioral intelligence modeling and machine learning automatically detects and prevents accidental, negligent and malicious data loss on email.Download Now