Credential harvesting via phishing remains a significant threat to organizations. In early February 2022, we detected a credential harvesting campaign leveraging a fake Microsoft Outlook login page. Although Secure Email Gateways (SEGS) have URL rewriting protection capability, these types of phishing efforts typically go undetected through the usage of obfuscation techniques such as using superscript tags hiding the malicious code.
Summary of the attack
An email impersonating Microsoft was sent using Amazon Simple Email Service targeting multiple individuals at a specific organization. The email informed recipients their password was due to expire and they needed to follow a link to reset it.
The link in the email followed multiple redirects before landing on a credential phishing site impersonating the Microsoft Outlook login page. Analysis of this attack reveals it to be related to known phishing as a service (PhaaS) site where anyone can purchase tools and services for phishing.
Email Content
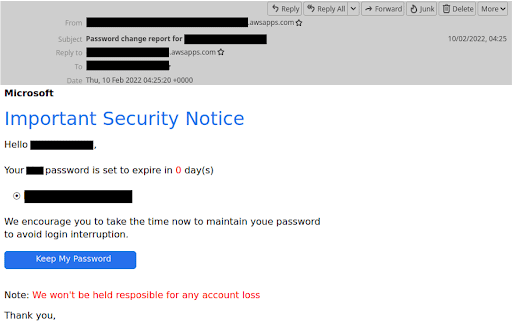
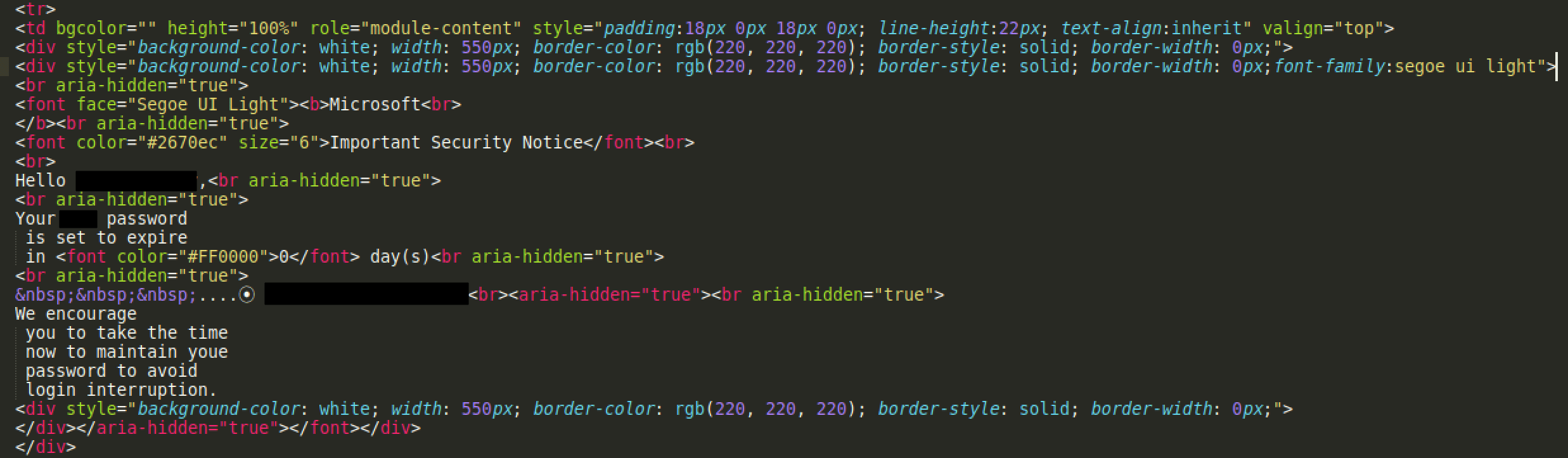
Below is a screenshot of the malicious email with a malicious link to reset the password. Note the usage of language (albeit with typos) expressing urgency around changing the end user’s password.
Screenshot of phishing email impersonating Microsoft
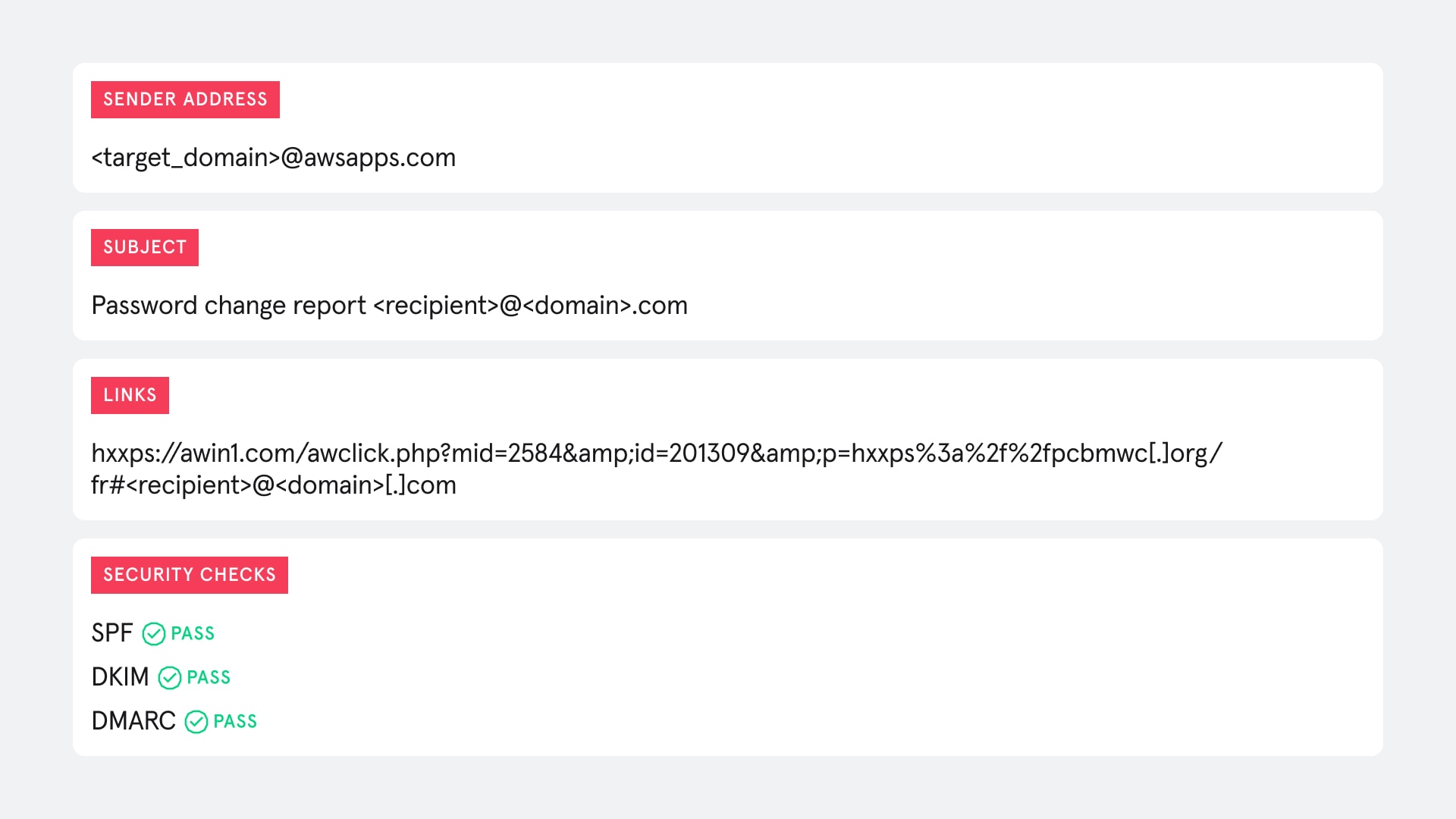
The threat actor sent the target recipients a request to change their Microsoft password that included a malicious link that would redirect to a credential harvesting website. Tailored to specific targets, the emails also appeared to be sent from an AWS Apps server using the Amazon Simple Email Service and passed security checks including SPF, DKIM and DMARC, meaning it is unlikely to be flagged as malicious.
Given the email appears to have been sent via Amazon SES, there is a chance the attacker may have compromised an AWS account. Alternatively they could have registered an account for the sole purpose of sending these emails and passing security checks since Amazon will be seen as a reputable sender.
Email body
When viewed from a mailreader these emails are fairly easy for the trained eye to spot. The main indicators being the grammatical errors that are common amongst phishing emails, as well as the suspicious link clickable from the button.
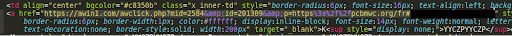
But underneath the message displayed was further evidence of the attacker going to great lengths through common phishing obfuscation techniques to make these emails difficult to detect.
The email body was base64 encoded which is not that uncommon for emails but still a technique attackers use to obfuscate the content of an email. Decoding this revealed the HTML used to construct the email. When focusing on the email body we find the attacker has added a series of HTML elements distributed randomly between the letters in the message.
Code snippet from HTML email body
Specifically the attacker has used superscript HTML tags to obfuscate the email body against common email security tools like SEGs.
-
<sup style=”display: none;”>YYCZPYYCZP</sup>
The attacker has added “display: none;” styling to each tag meaning the content of the element won’t appear in the displayed email. This means the recipient will only see the intended message displayed to them in a mail reader while making it difficult for legacy email security tools to pick up on any of the keywords that would indicate this as a phishing email.
Code snippet from HTML body with hidden sup tags remove
By removing the superscript tags from the code we can more clearly see the message left behind that was displayed to the recipient.
Phishing URL
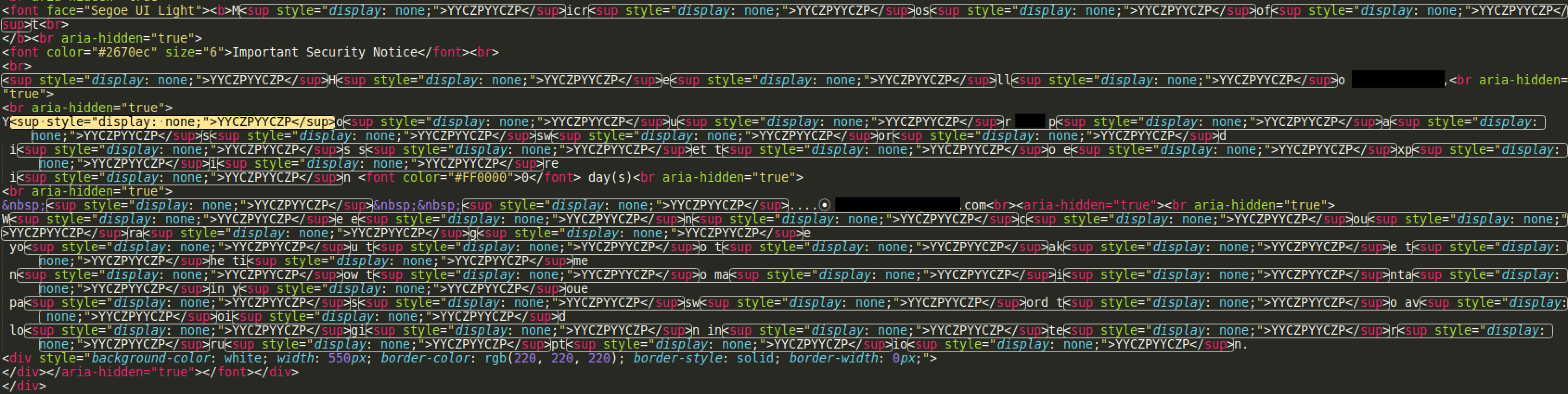
The email contained a phishing URL with the recipient address auto-populated at the end. The URL was added to a button labeled “Keep My Password”.
Phishing link embedded in HTML email body
The phishing link also contained a second URL nested in the query component of the first. The attacker is abusing an open redirect function in a well-known affiliate marketing network called Awin to redirect victims to the malicious site.
Phishing link from email:
-
hxxps://awin1.com/awclick.php?mid=2584&id=201309&p=hxxps%3a%2f%2fpcbmwc[.]org/fr#<recipient>@<domain>[.]com
Which redirects to:
-
hxxps://pcbmwc[.]org/fr#<recipient>@<domain>[.]com
The redirects are incorporated to bypass initial URL security checks common in legacy email security tools. Most security tools scanning URLs are likely to focus on the domain from the initial URL ‘awin1[.]com’ and recognise it as safe.
The domain in the nested URL ‘pcbmwc[.]org’ appears to belong to a buddhist monastery based in Patiya, Bangladesh. The site appears to be fairly basic and low budget, it is likely the attacker compromised this site and is using it to host part of their malicious infrastructure – an increasingly common tactic for phishing attacks.
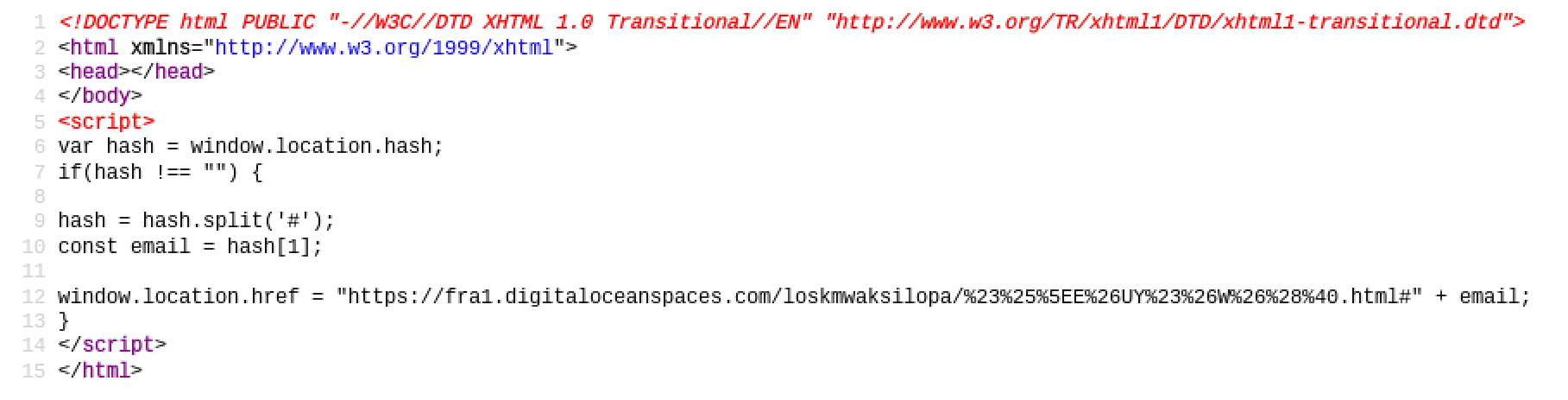
The initial URL leads you to an apparently blank page. The source code reveals there is a script checking to make sure there is still an email address present at the end of the URL after the ‘#’. This is intended to be the target’s email address.
Source code of webpage from first redirect
If there isn’t an email address appended to the end of the URL then nothing will happen and you will stay on the blank page. If there is an email address included at the end, then the script redirects the target to the final landing page for the phishing site with that email address still included in the URL.
Link to the final phishing site:
-
hxxps://fra1.digitaloceanspaces[.]com/loskmwaksilopa/%23%25%5EE%26UY%23%26W%26%28%40.html#<recipient>@<domain>[.]com
Phishing Site
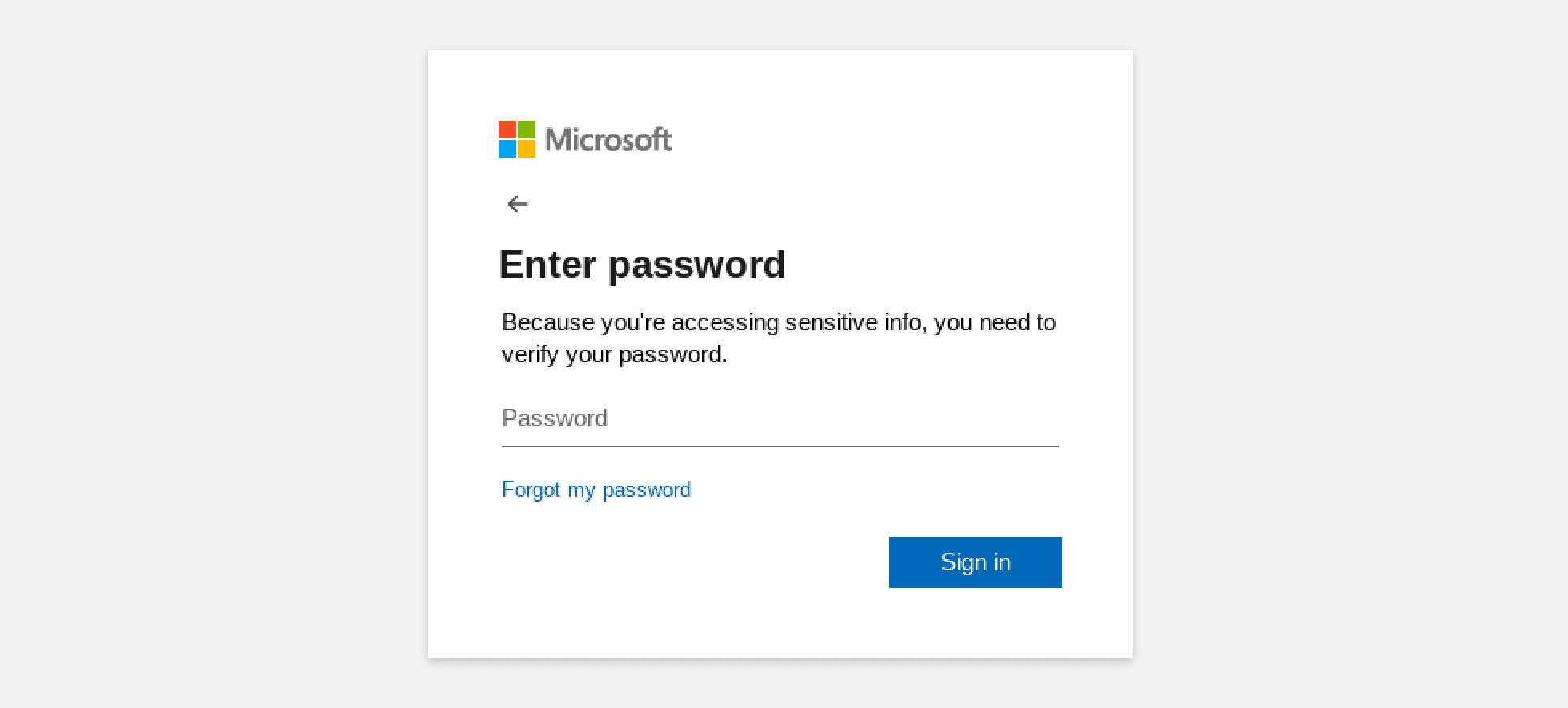
Clicking the link from the original email will lead to the page below with the target’s email captured in the URL. The site is designed to resemble the Microsoft Outlook login page where you are prompted to enter your password. Looking at the source code for this site, it appears to be based on a previously seen template also used for Microsoft credential harvesting but with a few alterations.
Screenshot of phishing site after 2nd redirect
To look as legitimate as possible, the site borrows graphics and styling directly from Microsoft owned CDNs. Entering a password into the box provided and clicking ‘Sign in’ would result in the email address from the URL and the password being captured and submitted through an AJAX post request to a php file hosted on a separate server.
PHP file:
-
hxxps://moliere[.]ma/aX3.php
The domain in the link to the PHP script appears to belong to a consulting firm based in Casablanca. If legitimate, then it too has likely been compromised by the attacker to host malicious infrastructure.
This script will most likely be what the attacker uses to harvest the credentials. It will either send the credentials to the attacker directly or store them in a location accessible by the attacker.
The source code of the site includes some jQuery scripts to perform a number of actions with the aim of making the site look and feel legitimate. This includes sections to provide feedback to the victim such as error messages and progress bars. One section checks to make sure the password entered isn’t blank and is more than one character long. Another section displays a fake progress bar after clicking sign in to give the illusion of a genuine login taking place.
If the credentials are submitted successfully then the victim is redirected to a genuine Microsoft login page and presented with the login screen again. The victim will assume that they entered their credentials incorrectly the first time and just carry on.
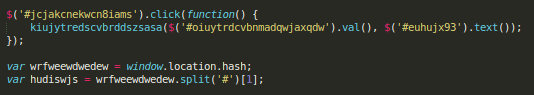
Another observation from the source code is that whoever wrote or borrowed the code has replaced most of the variable names and tag IDs with strings of seemingly random characters.
At closer inspection these random strings appear to be composed of various keyboard walk patterns. A keyboard walk is when you type a series of characters in the order they appear on the keyboard, for example ‘qwerty’ or ‘asdfg’. Often done by dragging a finger across the keyboard.
This has been done deliberately to make the code more difficult to read and follow without clearly labeled variables.
Code snippet from phishing site with keyboard walk variables
Phishing as a Service (PhaaS)
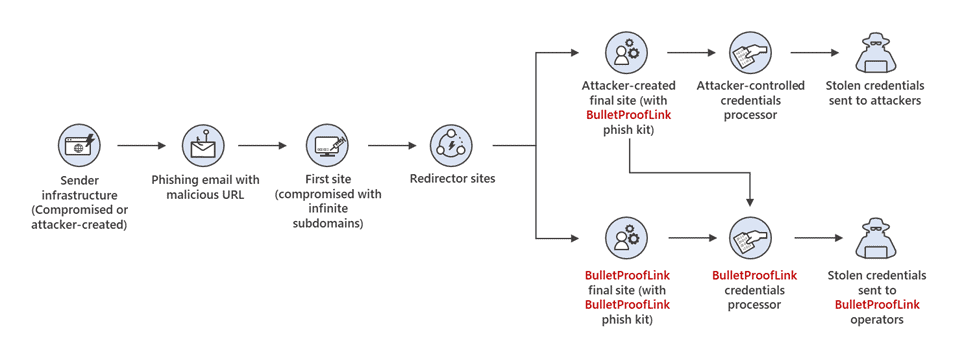
The primary features and indicators from this phishing attack point to it being related to the BulletProofLink (aka BulletProftLink) phishing as a service site, which was detected and analyzed by Microsoft in late 2021.
This site offers phishing kits for sale to anyone and also offers infrastructure to host and run malicious campaigns from. Phish kits or services will typically be available for sale for around $200.
Screenshot of BPL phishing styles page
Although there were some differences for the specific campaign analyzed here, the attack chain observed is virtually identical to that mapped out by Microsoft.
Microsoft: Attack chain of BulletProofLink enabled phishing campaign
This credential harvesting attempt is a good example of what is becoming a particularly common modus operandi to compromise an organization’s credentials and information system. The unfortunate reality is that such attempts have a high success rate of bypassing legacy and native email security controls. Threat actors are able to achieve this success through the use of obfuscation techniques that are tried and tested repeatedly against static, rule-based email security controls, until the desired outcome is achieved.
With continuously advancing sophistication of phishing attacks, it becomes a matter of when, and not if, an organization’s legacy email security controls will be circumvented.
Behavioral cybersecurity solutions like Tessian are increasingly seen as a gamechanger and a necessity to ward off advanced social engineering-based attacks. Tessian detects and prevents phishing attacks as the one discussed on a daily basis for our clients. It does this by scanning not only the URL links, but all of the fields contained in an email and contrasts this against a historical mapping of the email ecosystem to determine using machine learning, whether the email is malicious or safe. End-users then receive in-the-moment security warnings prompting them towards safer action.
Appendix: Indicators
Email Body (decoded)
- <sup style=”display: none;”>YYCZPYYCZP</sup>
URLs
- hxxps://awin1.com/awclick.php?mid=2584&id=201309&p=hxxps%3a%2f%2fpcbmwc[.]org/fr#
- hxxps://pcbmwc[.]org/fr#
- hxxps://fra1.digitaloceanspaces[.]com/loskmwaksilopa/%23%25%5EE%26UY%23%26W%26%28%40.html#
- hxxps://moliere[.]ma/aX3.php
Appendix: MITRE ATT&CK Framework
The tactics and techniques used by the threat actor can be inferred based on analysis of the email and the phishing site that was active at the time of receipt.
The attacker will have gathered email addresses to target either from data breaches dumped on the Internet or by scanning the target organizations’ public facing website for addresses, which will have most likely been found on their people page.
The attacker will either have developed or obtained the scripts and pages used to construct their malicious email through a phishing as a service site. It also appears they may have compromised vulnerable web-servers to host some of their malicious infrastructure used for harvesting credentials including the redirection page, the malicious login page and the PHP script to collect the credentials. This could also have been provided as part of a PhaaS package.
The attacker sent emails impersonating Microsoft containing a phishing link aimed at harvesting credentials. These emails were sent from an AWS Apps server via Amazon SES. Meaning the attacker may have compromised an existing AWS account or set one up for this campaign.
A number of techniques were employed to evade detection. The first is the use of Amazon SES to make emails appear reputable and pass security checks. The attacker also obfuscated the message in the email by placing hidden HTML elements at random intervals, making it difficult for security tools to pick up on keywords.
An open redirect was also used in the phishing URL to send the recipient to the malicious site via a trusted one first. Security tools and the recipient will often see the domain for the trusted site and assume the URL is safe.
Charles Brook
Threat Intelligence Specialist