The global COVID-19 pandemic has wreaked havoc on job markets. In the US, the unemployment rate stands at 6.2 percent and in the UK, it’s estimated that around 2.2 million people, or 6.5% of all workers, could be unemployed at the end of the year.
Cybercriminals are taking note.
When Tessian researchers analyzed suspicious emails relating to ‘unemployment’ and terms associated with unemployment that were flagged by our inbound solution Tessian Defender, they saw a notable spike in suspicious emails related to unemployment and COVID-19 in the week of 24th February – the week in which President Biden announced the third round of stimulus checks, which would send billions of dollars to people without jobs.
Our researchers also noted a spike in suspicious activity during the week of 8th March which is when COVID-19 the stimulus checks started being received. They found that:
- In the week of 24th February, the number of suspicious unemployment and COVID-19 related emails was 40% higher than the weekly average of such emails detected since the start of 2021. The number of unemployment themed emails alone was 16% higher than the weekly average.
- In the week of 24th February, the number of unemployment and COVID-19 related emails was 50% higher than previous week.
- In the week of 8th March, the number of suspicious unemployment and COVID-19 related emails was 51% higher than weekly average recorded since the start of 2021. The number of unemployment and COVID-19 related emails detected during this week was 69% higher than the previous week.
Over the last 12 months, cybercriminals have capitalized on the fear, uncertainty and doubt created by the global pandemic to make their scams as believable and convincing as possible. At the start of 2021, for example, Tessian reported a surge in newly registered domains related to the vaccine roll-out and confirmed that a number of these websites were malicious and designed to harvest people’s financial information and account credentials.
Now, cybercriminals are launching scams to prey on people who are vulnerable, out of work and urgently looking for relief. They are well aware that these individuals may be applying a little less scrutiny to the messages they receive – especially if the emails appear to have come from a legitimate and trusted sender.
How do unemployment scams work?
Here’s how a typical unemployment related scam works:
- A fake job posting is listed on legitimate job sites. Often, scammers will target small businesses to spoof or impersonate as it is less likely for these companies to monitor their job listings.
- An applicant will respond to that ad and will be sent a generic email asking them to perform a task for the interview process. These phishing emails could contain malicious attachments that applicants are asked to download or links to fake websites that ask applicants to input sensitive or personal information. This information could, then, be used to commit identity fraud.
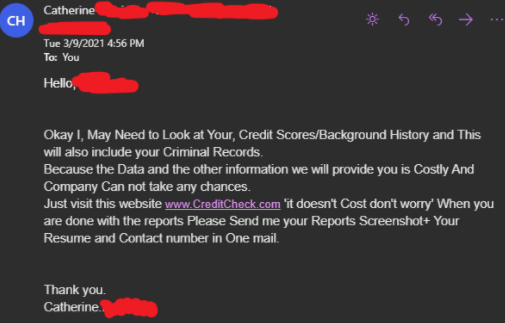
- Scammers will also ask applicants to click on a link that refers them to a fake credit check website. Here, they will ask the applicant to share financial information or wire money.
Cybercriminals can also identify targets via social media sites like LinkedIn. A recent report from Tessian found that 93% of people share job updates online, and while it’s common for people to let their networks know that they’ve been laid off and are looking for jobs, they are also unknowingly giving cybercriminals the information they need to craft convincing social engineering attacks that are designed to steal personal information.
The FBI has released warnings of unemployment scams, disclosing that many U.S. citizens have been victimized by bad actors “impersonating the victims and using the victims’ stolen identities to submit fraudulent unemployment insurance claims online.” In fact, figures from a watchdog for the U.S. Department of Labor reveal that Americans have lost a shocking $63 billion of unemployment funds during the pandemic to improper payments and fraud, while the Illinois Department of Employment Security reports having stopped around 1.1 million claims involving identity theft in the past year.
In many cases, victims don’t even realize they’ve been targeted until they later try to file for unemployment insurance benefits, receive a notification from the state unemployment insurance agency or even get notified by their employer that a claim has been filed while the victim is still employed.