In today’s fast-paced digital era, businesses are continually seeking ways to enhance productivity, streamline operations, and improve data security. Email communication has experienced drastic transformation with many businesses leaving behind on-premises legacy systems to experience the benefits of the cloud.
But choosing the right email security solution can seem daunting. WIth countless platforms offering protection from evolving cyber threats, it seems almost impossible to keep up or know what to choose. You might be asking the question, “How do these products work with my current tech stack?” or “Is my business ready to make the leap?” This blog will act as a guide, showing how complete cloud email security can support businesses at each stage of their digital transformation journey while ensuring robust protection.
Stage 1: Assessing the need for change
The first step in transitioning to the cloud is recognizing the limitations of a legacy system. On-premises email providers require extensive hardware investments, maintenance, and IT resources to keep them running smoothly. They may lack scalability, flexibility, and advanced security features required to combat evolving cyber threats. By evaluating these shortcomings, businesses can begin the shift towards a cloud-based system.
Stage 2: Choosing the right cloud providers
Before the migration, it’s important to understand your lineup of technology tools. What solutions will you need on-top of your email provider? Which integrations will make the transition seamless and extra valuable? Let’s start with Microsoft.
When selecting the right cloud provider, you’ll want to look for a track record in email security. Look for data encryption practices, infrastructure redundancy, and perhaps most importantly, protection against email attacks and data breaches.
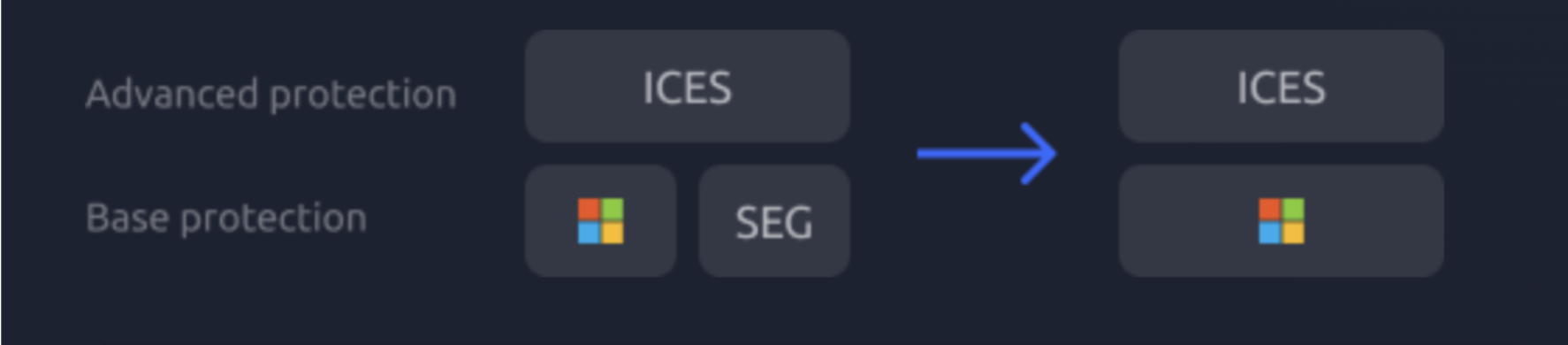
For base-level protection, businesses may layer a secure email gateway (SEG) on top of their email provider. The SEG works with Microsoft to provide rule-based protection against attacks. But rules can’t catch everything. An integrated cloud email solution can catch the advanced attacks that bypass Microsoft and a SEG.