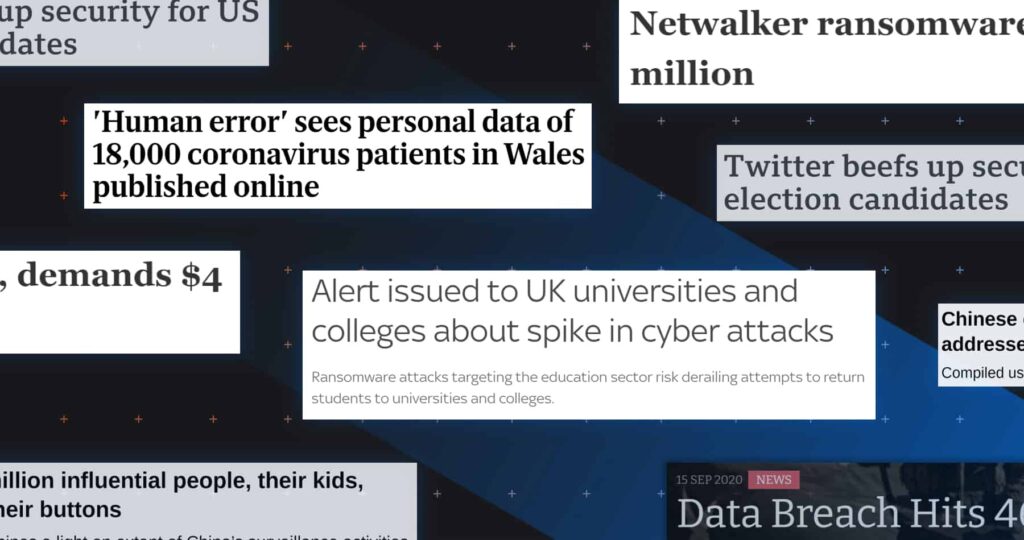
We’re back with another monthly roundup of cybersecurity news. Cybercriminals have once again been busy, with several high-profile data breaches and ransomware attacks occurring throughout September. And – rather unsurprisingly – social media platforms Twitter and TikTok have made the cut for the third month running.
Here are the top cybersecurity stories from September 2020, including links to further information. Need to catch-up? Check out headlines from July and top stories from August on our blog.
Research and advisory firm Gartner (who recently named Tessian a Cool Vendor) predicted this month that 75% of CEOs could hold personal liability for “cyber-physical” attacks by 2024.
Cyber-physical attacks aim to impact the “real world,” including critical infrastructure, internet of things devices, and healthcare equipment. Such attacks can result in physical injury and death. Gartner predicts that that cyber-physical attacks will cause up to $50 billion of damage by 2023
So what if Gartner is right? It would mean that if a company suffers a cyberattack resulting in physical harm — and it turns out that the company has not implemented appropriate cybersecurity measures — the company’s CEO could have to pay fines with their own money.
Gartner’s research tells us what every effective business leader already knows — an effective cybersecurity program is an essential requirement for every organization. If a cyberattack occurs, the buck stops with the company’s senior executives.
On September 6, Argentina temporarily stopped allowing people to cross its borders after the Netwalker ransomware hit the country. The attackers encrypted government migration data and demanded 355 Bitcoins (around $4 million) to unencrypt it.
This cyberattack led to chaos across border checkpoints — but the Argentinian government told domestic news website Infobae that it had no intention of negotiating with the hackers.
Ransomware continues to cause havoc worldwide, and it appears the problem is only getting worse. Research by SonicWall recorded approximately 121 million ransomware attacks in the first half of 2020.
The US Veterans Association (VA) announced this month that the personal information of around 46,000 military veterans had been “accessed by unauthorized users.” The cybercriminals aimed to “divert payments” intended for healthcare providers.
The VA’s financial services team wrote to the affected individuals to advise on how to mitigate the effects of the breach and offer free access to credit monitoring services.
The VA serves veterans all over the US. Strict new data breach laws in several jurisdictions — including New York, Washington DC, and Oregan — mean that the VA could face huge fines given the breach’s context.
Want to know more about US data security laws? Read our guidance for security leaders.
In a new report – The Future of Hybrid Working – Tessian reveals that IT leaders and employees both believe the future of work will be remote or hybrid. But, it’s clear this shift won’t be easy. Check out some of the key stats below:
- 82% of IT leaders believe employees are at greater risk of phishing attacks when working remotely
- Over a third of IT leaders are worried about their teams will stretched too far in terms of time and resource
- Half of emoployees have been working on their personal devices since March 2020
- Nearly 75% of employees said they received a phishing email while working on a personal device between March and July 2020….and 68% admitted to clicking a link or downloading an attachment within that email
- 78% of IT leaders think their organization is at greater risk of insider threats if their company adopts a permanent hybrid working structure
Read the full report to learn more and to understand how business can balance flexibility and security without draining IT teams’ resources.
A massive data breach occurred in Wales this month when the personal information of 18,105 coronavirus patients was leaked following an “individual human error.” The breach affected every Welsh resident who tested positive for COVID-19 between February 27 and August 30.
Public Health Wales said that the data included the “initials, date of birth, geographical area, and sex” of the affected individuals. In nearly 11% of people, though, the data also included the name of the nursing home or other healthcare setting in which the individual lived.
The data was uploaded onto a public server, where it was accessible and searchable for around 20 hours. It was viewed 56 times throughout this period.
Human error is a key cause of data breaches. Statistics show that around 88% of data breaches start with human error, and almost half of all employees believe they have made an error at work leading to security repercussions.
An academic at Fulbright University, Vietnam, has uncovered a vast Chinese database containing personal information of around 2.4 million people and their families. It looks like these individuals are “people of interest” to the Chinese Communist Party (CCP).
The company responsible for maintaining this huge database “provides big data analytics as well as other functionality to support Chinese military and intelligence analysts,” according to a research paper.
The research also suggests that the CCP uses the data for “intelligence, military, security, and state operations in information warfare and influence targeting.”
The database is believed to provide a way for the CCP to influence people in target sectors. It may be one of many such databases maintained by Chinese companies.
Much of the information in the database has been gleaned from publicly-available sources. The Chinese database is yet another important reason you should consider limiting the amount of personal information you put online.
You can learn more about how hackers are using open-source recon for deepfakes and other social engineering attacks from Elvis M. Chan, Supervisory Special Agent at the FBI and Nina Schick, Author of “Deep Fakes and the Infocalypse: What You Urgently Need to Know”, who both joined us at Tessian Human Layer Security Summit.
You can access their session “Safeguarding the 2020 Elections, Disarming Deepfakes via HLS On-Demand.
Following its spear phishing incident this July, Twitter has announced enhanced account security for certain “high-profile accounts” throughout the US election.
Twitter said that various types of accounts, including those belonging to US politicians, campaign officials, and political journalists, would receive the security enhancements from September 17.
So what’s changing? First, affected users must create “strong passwords,” of at least ten characters in length. They will need to confirm password reset requests via email. The affected users will also be “strongly encouraged” to enable two-factor authentication (2FA).
But that’s not all. Recall that the July spear phishing incident involved “internal support tools” — it wasn’t primarily an issue with users’ account passwords.
To address this, Twitter also states that it will improve internal monitoring of the affected accounts, including by using “more sophisticated detections and alerts,” “increased login defenses,” and “expedited account recovery” processes.
Want to know how to avoid the issues Twitter faced this July? Read our guidance on “vishing” attacks.
On September 27, Universal Health Services (UHS) – a Fortune 500 hospital and healthcare services provider that serves 3.5 million patients a year – was the target of a cyberattack that disable multiple antivirus programs and left hospitals around the country without access to computer and phone systems.
According to employees, files were being renamed to include the .ryk extenstion, computers’ screens changed, and – eventually – shut down, leaving them without access to anything computer-based. And, in response to the attack, employees were told to shut down all systems to block attackers’ from reaching more devices on the network.
While UHS hasn’t made a statement, the logistics of the incident suggest ransomware. That means patient and employee data is at risk.
The US Federal Energy Regulatory Commission (FERC) and the North American Electricity Reliability Corporation (NERC) have released a report advising energy providers on creating an Incident Response and Recovery (IRR) plan for cyberattacks.
The report is based around an existing cybersecurity framework: the National Institute of Standards and Technology (NIST) Special Publication 800-61, also known as the Computer Security Incident Handling Guide.
Governments appear to be increasingly concerned about the cybersecurity of critical infrastructure. This concern is well-founded — in 2019, 90% of security professionals surveyed across the utilities, energy, health, and transport sectors reported that their organizations had faced at least one successful cyberattack.
Much of the advice to energy providers is good practice across all sectors. FERC and NERC recommend a four-part framework, consisting of security controls relating to preparation, detection and analysis, containment and eradication, and post-incident activity.
As students worldwide return to schools, colleges, and universities, education providers are most concerned with defending against a COVID-19 outbreak. But the UK’s National Cyber Security Centre (NCSC) gave a stark warning about a different type of threat: ransomware.
The NCSC’s alert describes “recent trends observed in ransomware attacks” targeting the education sector, which the agency says are increasingly common. The guidance follows a series of ransomware attacks against universities in the UK, US, and Canada this July.
The agency warns that cybercriminals are exploiting out-of-date software and are accessing remote desktop protocol (RDP) software using credentials stolen via phishing attacks. It also warns that phishing emails are being used to deploy ransomware.
So how does the NCSC recommend education providers protect themselves? The same ways all cyber-secure organizations protect themselves — including ”disrupting ransomware attack vectors” by implementing phishing defenses, and “enabling effective recovery” by keeping backups of data.
Implementing DMARC is also essential to prevent brand impersonation and successful spear phishing attacks. And, according to Tessian research, 40% of the top 20 US universities aren’t using DMARC records.
On September 21, US President Trump said he had approved the sale of part of ByteDance, the parent company of video-sharing platform TikTok, to Oracle and Wal-Mart. The deal temporarily averts harsh restrictions on TikTok set out by the US Department of Commerce three days earlier.
The sale results from an executive order issued by President Trump in August, stating that the TikTok app “captures vast swaths of information from its users, including… location data and browsing and search histories.” TikTok maintains that this activity is standard industry practice.
The US companies could take a collective 20% stake in ByteDance, with Oracle hosting TikTok user data in Oracle Cloud. Some analyses suggest that security-conscious nations and businesses are increasingly likely to implement these sorts of “data localization” measures.
Trump had previously assured the public that TikTok would be “totally controlled” by the US firms. However, the president assured a press conference that the companies would be using “separate clouds and very, very powerful security.”
That’s all for this month. If we missed anything, please email madeline.rosenthal@tessian.com and stay tuned for the next roundup. Don’t forget: You can easily share this on social media via the buttons at the top right of this post.