For most security leaders and SOC teams, “visibility” is the holy grail. It makes sense…
Why does visibility matter?
Clear visibility of threats is the first step in effectively reducing risk. It’s what makes analyzing, correlating, reporting, and proactively preventing security events possible. It’s what allows security teams to find the needle in the haystack. That’s why Splunk is so valuable, and why it’s essential security solutions easily integrate with SIEM (pronounced “sim”) systems.
Looking for some tips and tricks to help you and your team get the most out of your data in Splunk?
We talked to Imraan Dawood, Information Security Officer at Investec, and Martin Nortje, Information Security Engineer at Investec, about how they use Splunk to level up their security, without over-burdening their SOC teams.
We’ve captured the highlights below.
7 tips for SOC teams using Splunk
1. Don’t create too many dashboards
For those who have the tool, Splunk is the front door for all analytics for SOC and data security teams. It’s the first thing they log into when they sit down at their desk, and the one place they can see security events pulled from across their security stack.
According to Imraan and Martin, it enables SOC teams to pinpoint potential problems in a matter of minutes or seconds versus hours or days. But, too much information or “noise” can be overwhelming and counterproductive.
So, instead of tracking everything, be choosy. Imraan and Martin suggest that SOC teams work backward. First, consider what would be most valuable for analysts to see. Then, consider what you need to filter out in order for them to see that at a glance. (See point 2….)
2. Create a “hit list” of words and terms to help you zero in on the events that could have the biggest business impact
While – yes – SOC teams will want to have visibility of all security events, it’s important to take the time to plan the structure and layout of the information in your dashboards to ensure you have an accurate picture of the security landscape and to help quickly identify high-impact threats – for example, misdirected emails.
Not all misdirected emails are created equal, though.
Let’s say Donna, a sales executive, accidentally emailed the wrong Brad to ask “Can you still make the call at 2:00?”. Now, let’s say Elaine, a Finance Director, accidentally emailed the wrong Todd financial projections for Q2 2021. Which requires more immediate attention? Which could have the biggest business impact? The latter.
I
mraan and Martin suggest that SOC teams create a “hit list” of words and terms – for example, those related to financial data, PII, or R&D – to get a better view of what really matters.
Here’s how you do that:
- Make a list of the keywords and terms that you would like to report on
- Perform a search for those terms within Splunk to verify that the search term is only yielding the results that you’d like to alert on. (Doing this will ensure that you aren’t generating unnecessary noise for your SOC teams and will reduce notification fatigue.)
- Configure an alert to search and identify those specific keywords and terms within the platform.
Looking for more details? Check out this article from Splunk: Save your search as an alert
3. Remember that you can’t automate everything
Splunk is great because it automatically integrates data from endpoints, applications, servers, etc. It makes life much easier for data analysts and the rest of the security team. But you can’t automate everything. For example, what happens after Elaine, the Finance Director, accidentally sends that email with financial projections to the wrong Todd?
Several teams will have to be involved, from HR, to Customer Success, to Legal. It’s difficult – if not impossible – to automate those processes and workflows completely. To put it simply, follow-up will still be manual. Top tip from Imraan and Martin: Automate your case management instead.
4. Consider the “why” and the “how” just as much as the “what”
We all know that employees can make mistakes. Whether it’s cc’ing someone instead of bcc’ing someone, logging onto an unsecured network, or re-using a password. But, some employees aren’t simply acting negligently. They’re acting maliciously. And, it’s essential SOC teams can differentiate between the two. The question is: How?
Imraan and Martin suggest relying on historical data. After all, it takes multiple insights to understand what’s business as usual vs. something more malicious. For example, if you’ve had an incident of a “bad leaver” in the past, use that data to compare and “match” the same behavior in real-time.
What does a “bad leaver” look like? Are they sending 1 email to a personal account a day over the course of 2 months? Or are they sending 15-20 emails a day for a week? Are they including attachments or not?
5. Be thoughtful in what data you include in reports for specific teams
As we’ve said, Splunk makes reporting easy. But, to effectively communicate risks (and wins!) and actually influence change, you have to be thoughtful in what data you include in reports for specific teams. Your Risk Committee and your CEO will care about different things.
A few things you should consider when preparing reports:
- How much do they know about cybersecurity?
- What’s most relevant to their day-to-day?
- What metrics and KPIs are they held accountable for?
- What’s the organization’s risk tolerance?
6. Lean on the vendors in your security stack for queries
Most vendors understand the importance of capturing security events in SEIM and will have advice on best practices and use cases that they’ve seen work well for other customers.
Are you a Tessian customer? If you didn’t already know, we’ve created dozens of articles and guides for customers to make sure they get the most out of our products via Splunk. Just log into the Help Center or shoot your Customer Success Manager a message.
7. Use the insights!
Last but certainly not least, Imraan and Martin made it clear that viewing the data in Splunk is just step one. Step two is actually implementing processes that help reduce security incidents and improve the organization’s security posture.
For example, if you saw a massive spike in the number of employees who were printing sensitive documents or sending attachments to personal devices immediately after the move to remote-working, you might want to consider reminding employees or existing policies or – better yet – creating new policies that enable them to do their jobs without breaking the rules.
The key is to combine data-centric and human-centric approaches to really effect change.
Learn more about Tessian’s integrations
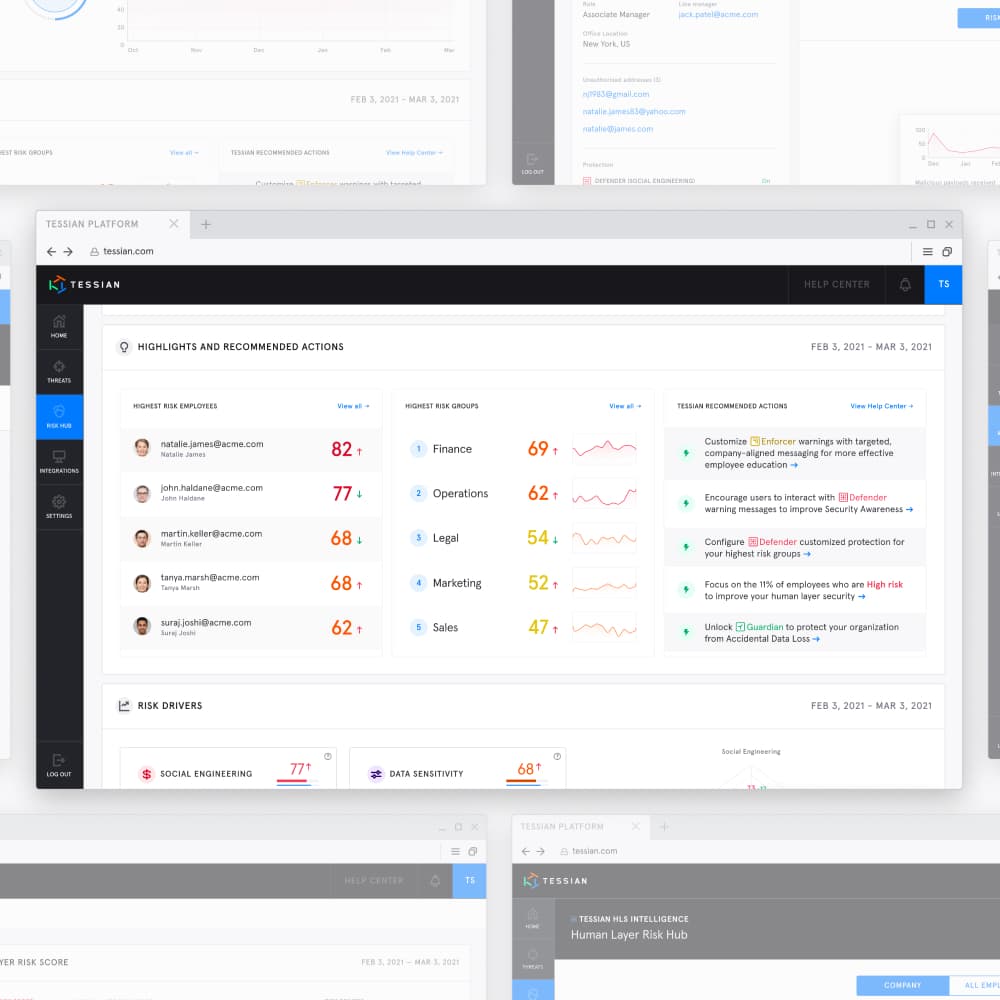
Tessian’s Human Layer Security (HLS) platform has vast integration capabilities to help security teams achieve increased visibility and extended protection.
Learn more here.
Or, if you’re looking for more tips, subscribe to our newsletter below.