Ransomware is a widespread, serious threat. So far in 2021, we’ve seen ransomware attacks on hospitals, gas pipeline operators, and software firms supplying thousands of businesses.
And the situation is getting worse. Research suggests that the overall cost of a ransomware attack doubled in the past year, rising from $761,106 in 2020 to $1.85 million in 2021—and that the global total cost of ransomware could exceed $265 billion per year by 2031.
This article will explain what ransomware is and how ransomware spreads. We’ll then analyze a recent ransomware attack to help you understand how this serious form of cybercrime works.
Types of ransomware attack
There are two main types of ransomware attacks. Both involve the victim downloading a malicious ransomware program.
In the first type of ransomware attack, the malicious program encrypts the victim’s files, rendering them unreadable and unusable. To decrypt their files, the victim must pay a ransom—or else they’ll never be able to access them again.
In the second type of ransomware attack, the malicious program transfers the victim’s files to the attacker. In this type of attack, the victim must pay a ransom to prevent their files from being published on the open web.
Either type of ransomware attack is avoidable. But ransomware can be devastating for any business, leading to extortion, recovery, and mitigation costs—not to mention a loss of your company’s time and reputation.
How is ransomware delivered?
For a ransomware attack to succeed, the threat actor must find a way to get the malicious ransomware program onto their target’s device. Let’s take a look at three keys ways of achieving this.
Social engineering attacks
Social engineering attacks—such as phishing, spear phishing, or Business Email Compromise (BEC)—are normally cited as the leading cause of ransomware infection.
In a typical social engineering attack, the target receives a malicious email encouraging them to click a download link or download an attachment. While the email may look trustworthy, it contains a payload in the form of a ransomware file.
The notorious “Ryuk” strain of ransomware spreads mostly via social engineering attacks. Security experts estimate that the Ryuk ransomware has earned cybercriminals over $150 million in ransom payments from companies worldwide.
Remote Desktop Protocol
Remote desktop protocol (RDP) enables a third party to take remote control of a person’s computer.
RDP has legitimate uses, including enabling IT support services to troubleshoot software issues. But once a cybercriminal has admin access to your system, they can do pretty much whatever they want—including carrying out a ransomware attack.
RDP was the root cause of several high-profile ransomware attacks, including the SamSam ransomware that forced Atlanta’s public authorities to pay out nearly $6 million in 2018.
Drive-by website download
A drive-by download attack occurs when a person downloads and installs a malicious file, for example via a website that has requested permission to download an executable file, Javascript applet, or ActiveX component.
When the victim clicks “Save” or runs the malicious download—whether due to carelessness or because they believe the file is legitimate—the ransomware installs itself and takes over their computer.
Analysis of a ransomware attack
Here’s a recent example of a ransomware attack, to help you understand this devastating form of cybercrime works.
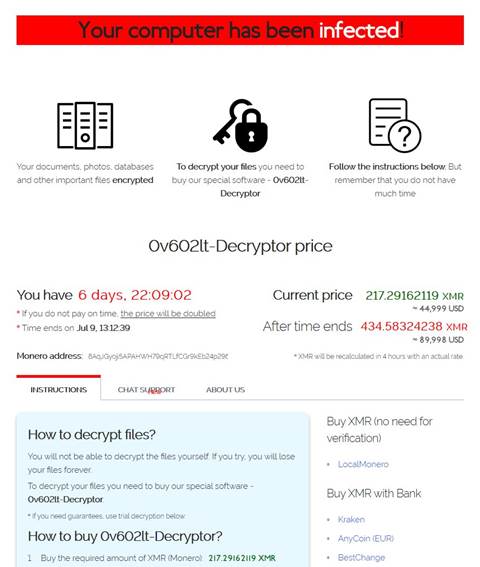
On July 3, 2021, hours before the long Independence Day weekend started in the U.S., thousands of workers got a message on their computer screens: “Your computer has been infected!”
These infected computers had recently installed an update of IT management software Kaseya—an update that had been infected with the REvil ransomware. This type of “supply chain” attack is an increasingly common vector for malware.
Here’s the ransom note that workers saw (shortly before they’d planned to go home for the holidays):