Solution Briefs
Stop Account Takeover with Tessian Defender
Detect and prevent risks originating from compromised email accounts in third-party partner, vendor and customer networks.
Download the ATO datasheet to learn…
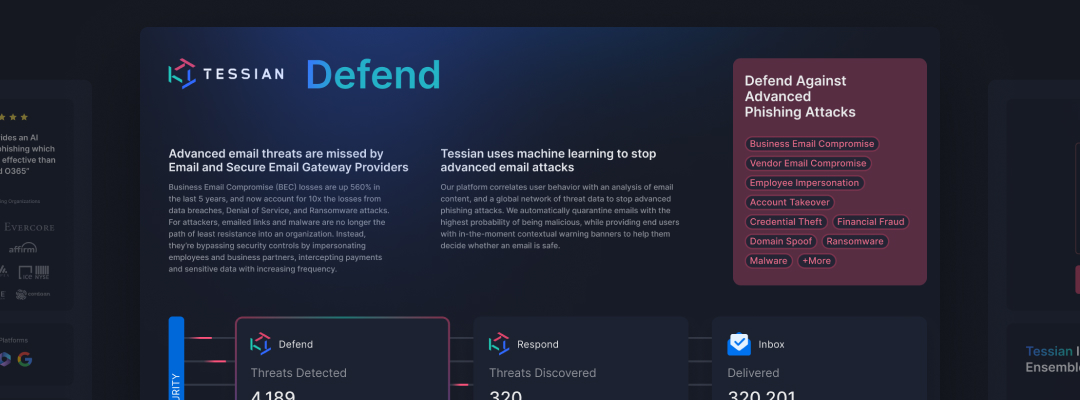
- What is Account Takeover and how it’s one of the top pathways to Business Email Compromise (BEC)
- The top reasons why Account Takeover attacks are so difficult to detect
- Why the adoption of cloud office systems from Microsoft and Google continues to grow is forcing security and risk management leaders to evaluate the native capabilities offered by email security products
- Solution differentiators: How Tessian Defender detects and prevents Account Takeover attacks