That’s a wrap! A big “thank you” to our incredible line-up of speakers, panelists, sponsors, and – of course – attendees of Tessian’s fifth Human Layer Security Summit.
Security leaders shared advice on scaling enterprise security programs, explained how they’ve successfully re-framed cybersecurity as a business enabler, and offered tips on how to prevent breaches.
If you’re looking for a recap, we’ve identified one key takeaway from each session. You can also watch the Summit (and previous Summits…) on-demand for free here.
Want to be involved next time? Email us: marketing@tessian.com
1. The average person makes 35,000 decisions a day – one mistake could have big consequences
While most decisions you make won’t impact your company’s cybersecurity, some can. For example, sending an email to the wrong person, misconfiguring a firewall, or clicking on a malicious link. And these mistakes happen more often than you might think…
95% of breaches are caused by human error.
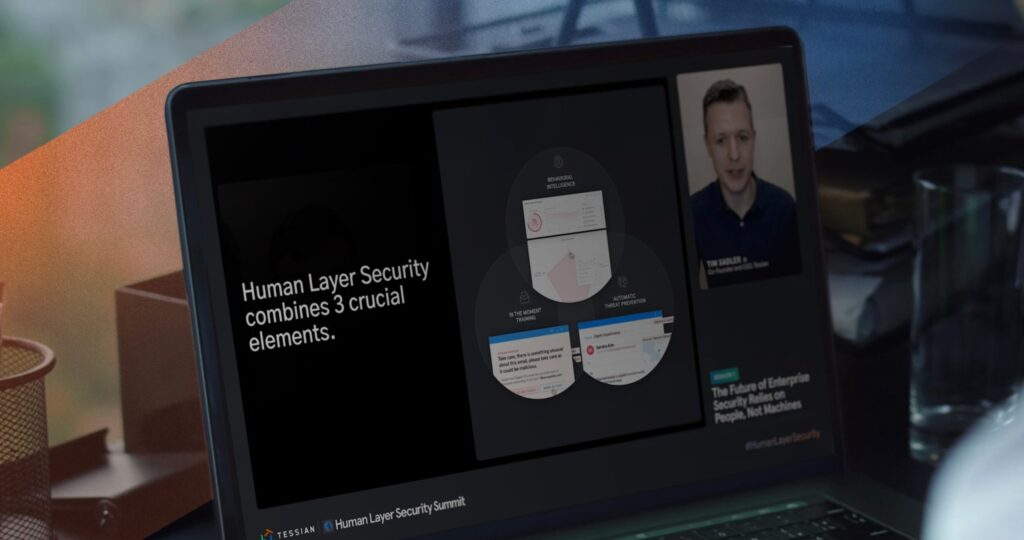
That’s why security leaders implement policies, offer training, and deploy technology. But did you know there’s one solution that prevents human error by offering automatic threat prevention, training, and risk analytics all in one platform?
Watch the full session below to hear more about Tessian Human Layer Risk Hub, or download the datasheet for a more detailed look at the product.
Further reading:
- Research: Why Do People Make Mistakes?
- What is Human Layer Security?
- Product Datasheet: Tessian Platform Overview
2. The best cybersecurity strategies combine experience, threat intelligence, and business intelligence
If you’re looking for practical advice, check out this session. Bobby Ford, Senior Vice President and CSO at Hewlett-Packard, and James McQuiggan, Security Awareness Advocate at KnowBe4, discuss cybersecurity strategies they recommend for the enterprise.
You might be surprised to find out that technology wasn’t the focus of the conversation. Relationships were. By listening to and understanding your people, you can build better relationships, ensure alignment with the company’s mission, vision, and values, and influence real change.
“You have to assess the overall culture and then develop a strategy that’s commensurate with that culture,” Bobby explained.
For more insights – including a personal anecdote about how implementing a security strategy is like teaching your children to walk – watch the full session.
Further reading:
- 7 Fundamental Problems With Security Awareness Training
- Hey CISOs! This Framework Will Help You Build Better Relationships
3. Some of the year’s biggest hacks have one thing in common: human error
Who better to discuss this year’s biggest hacks than a hacker?
Samy Kamkar, Renowned Ethical Hacker, joined us to break down the SolarWinds and Twitter breaches and offer advice on how to prevent similar incidents.
To start, he explained that in both hacks, social engineering played a role. That’s why people are the key to a strong and effective cybersecurity strategy.
Sure, automated detection and prevention systems can help. So can password managers. But, at the end of the day, employees are the last line of defense and hackers don’t attack machines. They attack people.
According to Samy, “We don’t have time to implement every possible safeguard. That’s why we have to lean on training.”
Watch the full session for more insights, including Samy’s book recommendation and why he doesn’t trust MFA.
Further reading:
- Tessian Threat Intelligence and Research
- Real World Examples of Social Engineering
- Research: How to Hack a Human
4. DLP is boring, daunting, and complex….but it doesn’t have to be
Punit Rajpara, Global Head of IT and Business Systems at GoCardless, has a strong track record of leading IT and security teams at start-ups, with a resume that includes both Uber and WeWork.
For him, empowerment, enablement, and trust are key and should be reflected in an organization’s security strategy. That means rule-based DLP solutions – which he deemed “boring, daunting – and complex” just don’t cut it.
Tessian does, though.
“Security is often looked at as a big brother, we’re-watching-everything-you-do sort of thing. At GoCardless, Tessian has changed that perception and is instead putting the power in the hands of the users,” Punit explained.
To learn more about why Punit chose Tessian and how he uses the platform today, watch the full session below.
Further reading:
- Customer Story: How Tessian Gave GoCardless Better Control and Visibility of Their Email Threats
- Research: Data Loss Prevention in Financial Services
- Product Datasheet: Tessian Platform Overview
5. Learning is only effective when it’s an ongoing activity
When asked what was top of mind for her when it comes to cybersecurity, Katerina Sibinovska, CISO at Intertrust Group simply said “data loss”. I think most would agree. But, as we all know, data loss can be the result of just about anything. Lack of awareness, negligence, malicious intent…
So, how does she prevent data loss? By balancing technical and non-technical controls and building a strong security culture.
And, as she pointed out, annual (and even quarterly!) training isn’t enough to build that strong security culture. “It can’t just be a tickbox exercise,” she said.
Instead, meet employees where they are. Add context. Engage and reward them. Support them rather than blame them.
To learn more about how she’s reduced data loss – and what role Tessian plays – watch the full session.
Further reading:
- Why Do the World’s Top Financial Institutions Trust Tessian?
- Pros and Cons of Phishing Awareness Training
- Product Data Sheet: Tessian Human Layer Risk Hub
6. People don’t just want to know WHAT to do, but they want to know WHY.
You don’t want to miss this Q&A. Jerry Perullo, CISO at ICE | New York Stock Exchange has over 25 years of experience in cybersecurity and shares his thoughts on the role of the CISO, how to get buy-in, and why training is (generally) a “time-suck” for employees.
His advice? Don’t just tell people what they need to do in order to handle data safely, tell them why they need to do it. What are the legal obligations? What would the consequences be? This will help you re-frame cybersecurity as an enabler instead of an obstacle.
Watch the full session for more tips from this cybersecurity trailblazer.
Further reading:
1.CEO’s Guide to Data Protection and Compliance
2. 7 Fundamental Problems With Security Awareness Training
You’re invited to the next Summit! Subscribe to our weekly newsletter to be the first to hear about events, product updates, and new research.