Remember last year’s SolarWinds attack? It was one of the most significant hacks in history and the fallout is ongoing. We may never know exactly how bad the attack was.
But, we do know that it’s making waves and was a wake-up call for many organizations—not least the U.S. government, which has realized just how vulnerable it is to hackers targeting the countless companies in its supply chain.
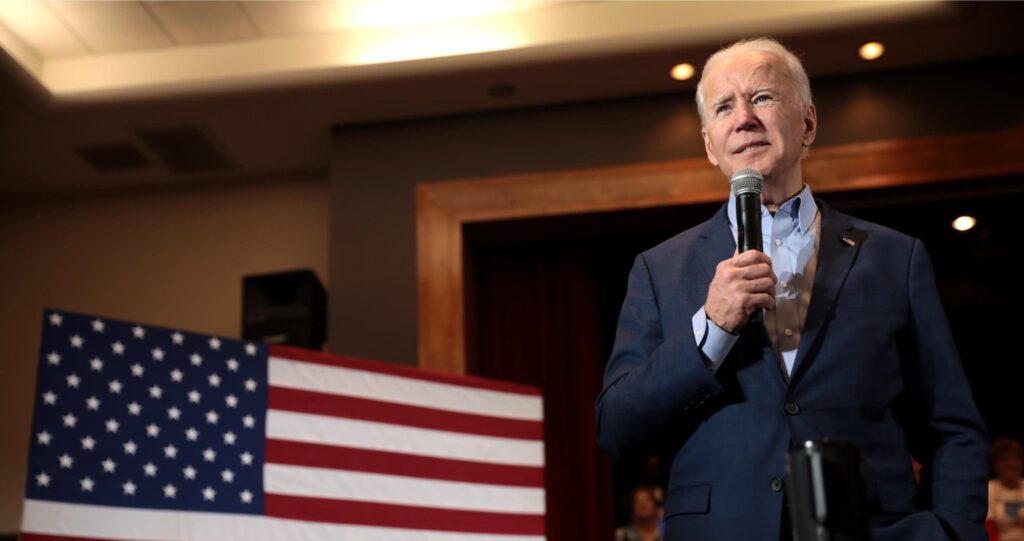
In response to SolarWinds, President Biden’s administration is drafting an executive order that aims to strengthen cybersecurity among both federal and private organizations.
We’ve combed through the available information about the upcoming executive order to help you understand the potential implications for your business.
🕵 What information do we have about the executive order?
We’ve had little communication from the White House about Biden’s upcoming executive order.
That means most of the information available derives from the following sources:
- The announcement that an executive order was in development, made in February by Anne Neuberger, White House deputy national security adviser for cyber and emerging technology
- A March speech made to the RSA Conference by Alejandro Mayorkas, secretary of homeland security
- A leaked draft of the executive order seen by journalists in March
- An April speech to the Cybersecurity Coalition, given by Jeff Greene, acting senior director for cybersecurity at the National Security Council
- Further comments from Neuberger to NPR, made April 29
The order will likely tighten the rules around the procurement of private-sector software and services by government agencies—or, as Neuberger puts it: “If you’re doing business with the federal government, here’s a set of things you need to comply with in order to do business with us…”
The means companies hoping to obtain or maintain government contracts, software developers, and government agencies will need to demonstrate that they have implemented certain security measures.
Don’t fall under any of the above three categories? Still worth paying attention. This executive order is a clear sign that the U.S. is taking cybersecurity seriously.
Now is the time to review your organization’s approach to cybersecurity—to ensure you have identified any vulnerabilities and can prevent or respond to attacks.
1. Breach notification
The order will likely include a breach notification rule that will impact companies supplying the federal government with software or hardware products.
Of course, companies doing business with the federal government aren’t the only organizations to be obligated to breach notification rules.
Data breach notification rules are common worldwide, particularly in Europe, where the General Data Protection Regulation (GDPR) obliges organizations to notify regulators and individuals in the event of a breach of personal data within 72 hours.
Further reading:
⚡ GDPR: 13 Most Asked Questions + Answers
⚡ Biggest GDPR Fines in 2020 and 2021
There is currently no generally applicable federal breach notification law in the U.S. But, many states and some sectors have breach notification laws. We look at several of these in our article US Data Privacy Laws 2020: What Security Leaders Need to Know.
The order’s breach notification rule would reportedly oblige federal contractors to notify a cyber incident response board (yet to be established) within days of a suspected hack or data breach. Organizations might also be required to cooperate with the FBI and the Cybersecurity and Infrastructure Agency (CISA) to investigate the incident.
Reuters suggested that the order might also contain a public disclosure rule. Public disclosure might involve notifying any members of the public affected by a data breach, either individually or via the media.
Note: Any organization operating under a data breach notification requirement must have robust and efficient procedures in place to identify and respond to a cybersecurity incident.
The sooner you can detect malicious activity, the sooner you can report it—and the sooner it can be contained or mitigated.
2. Software development security
The order will likely set out improved security requirements for software procured by federal agencies. This means developers of such software will need to implement stronger security standards in their products.
Software vendors supplying the federal government may be required to create a “Software Bill of Materials” (SBOM) accompanying their products. An SBOM acts as an inventory that provides details about the components of a piece of software.
Jeff Greene also reportedly suggested that National Institute of Standards and Technology (NIST) controls would play a role in providing improved security standards for government contractors.
It’s not clear whether software vendors would be required to comply with an existing NIST framework, or whether the government would work with NIST to derive new standards.
However, whether or not an organization supplies software to the federal government, compliance with a scheme such as the NIST Cybersecurity Framework is strongly recommended.
See our Beginner’s Guide to Cybersecurity Frameworks for more information.
3. Improved security within federal agencies
Finally, Biden’s executive order will likely include some mandatory security standards for government agencies and employees, including encryption of data and the use of multi-factor authentication (MFA).
These technical controls are basic, and they are already best practice for any organization handling personal or sensitive data. But mandating such controls by law is a significant step.
As we learn more, we’ll update this article. Want to be the first to know? Sign-up for our weekly blog digest, including global cybersecurity news, original research, and tips from security leaders.