Research & Reports
-
 Research & Reports
Research & ReportsForrester has named Tessian a Strong Performer in The Forrester Wave™: Enterprise Email Security, Q2 2023
-
 Research & Reports
Research & ReportsState of Email Security 2022
-
 Research & Reports
Research & ReportsHow Security Cultures Impact Employee Behavior
-
 Research & Reports
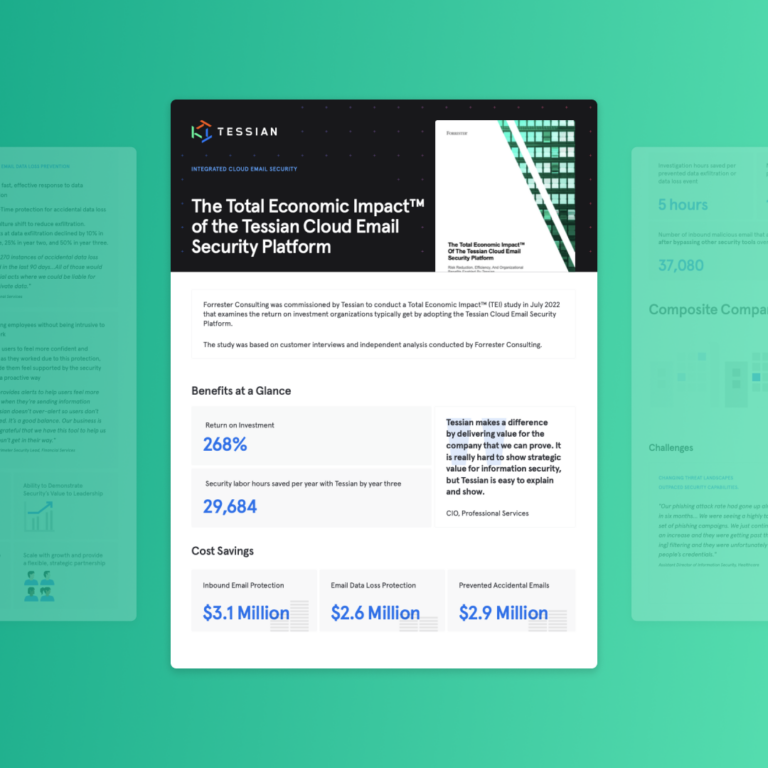
Research & ReportsForrester findings uncover a 268% ROI with The Tessian Cloud Email Security Platform
-
 Whitepapers
WhitepapersForrester Consulting findings uncover a 268% ROI over three years with The Tessian Cloud Email Security Platform
-
 Whitepapers
WhitepapersThe Ponemon Institute: Data Loss Prevention on Email in 2022 Report
-
 Research & Reports
Research & ReportsWhy Do People Make Mistakes That Compromise Cybersecurity?
-
 Research & Reports
Research & ReportsForrester Infographic: Take Control of Email Security with Human Layer Security Protection
-
 Research & Reports
Research & ReportsReclaiming Hours Lost to Cybersecurity Incidents
-
 Whitepapers
WhitepapersForrester Study: Take Control of Email Security with Human Layer Security Protection
-
 Research & Reports
Research & ReportsSpear Phishing Threat Landscape 2021
-
 Whitepapers
WhitepapersESG Whitepaper: Closing Critical Gaps in Microsoft 365 Native Security Tools
-
 Research & Reports
Research & ReportsHave Employees Picked Up Bad Security Behaviors While Working From Home?
-
 Research & Reports
Research & ReportsThe State of Data Loss Prevention in Healthcare
-
 Research & Reports
Research & ReportsThe State of Data Loss Prevention in Legal
-
 Research & Reports
Research & ReportsThe State of Data Loss Prevention in Financial Services
-
 Research & Reports
Research & ReportsOpportunity in Cybersecurity Report 2021
-
 Research & Reports
Research & ReportsHow to Hack a Human
-
 Research & Reports
Research & ReportsSecuring the Future of Hybrid Working
-
 Research & Reports
Research & ReportsThe Psychology of Human Error
- 1
- 2







