On Wednesday, July 29, Tessian hosted a webinar with two customers: Euromoney Institutional Investor and ERT. The topic? Data exfiltration and reduced visibility while workforces are remote.
Martyn Booth, Chief Information Security Officer (CISO) at Euromoney Institutional Investor and Ted Crawford, Chief Information Officer (CIO) at ERT both offered incredible insights about how things have changed from a security perspective over the last four months and how Tessian has helped them lock down email, even before their employees started working from home.
And, because Martyn and Ted are two security leaders in different industries (Financial Services and Tech/Healthcare respectively) and are based in different regions (England and The United States), they were able to share diverse opinions and experiences.
Keep reading to learn more about how Tessian has helped them solve some of their biggest pain points.
7 Problems Tessian Helps Solve
1. Tessian prevents accidental data loss on email
When you hear data exfiltration, what do you think of?
Many of you probably thought immediately about Insider Threats and other malicious activity. But, as our customers pointed out, most incidents involving data loss are accidental. Or, as Martyn put it, are the result of “naive email usage”.
It could be an employee sending an email to the wrong person (we call this a misdirected email), it could be someone hitting “reply all”, or it could be someone emailing a spreadsheet to their personal email account to work on over the weekend.
Harmless, right? Not exactly. If these “accidents” involve sensitive information related to employees, customers, clients, or the company itself, it’s considered a breach.
Organizations can prevent all of the above with Tessian Guardian.
This is especially important now that employees are working remotely. Why? Because the lines between peoples’ personal and professional lives are blurred. Beyond that, people are distracted, stressed, and tired which, as we’ve shown in our latest research report The Psychology of Human Error, increases the likelihood that a mistake will happen.
2. Tessian prevents malicious data exfiltration on email
While, many data loss incidents are accidental, some employees do intentionally exfiltrate data. There are a number of reasons why, but financial gain and a competitive edge are the most likely motivators.
Unfortunately, with so many people being laid off, made redundant, or furloughed, many organizations have seen a spike in this type of malicious activity.
But, with Tessian Enforcer, organizations’ most sensitive data is kept safe.
Employees attempting to email sensitive information to themselves or a suspicious third-party will receive a warning message, explaining why the email has been flagged and asking if they’re sure they want to proceed. At the same time, security teams will get a notification.
Note: Instead of warning the employee and asking if they’d like to send the email anyway, security teams can easily configure Tessian to automatically quarantine emails that look like data exfiltration. Book a demo to see Tessian in action.
3. Tessian makes it easy to report security risks and communicate ROI
Communicating cybersecurity ROI has historically been a real challenge for security leaders. Not with Tessian. Martyn explained how Tessian enables him to share key results with executives and demonstrate the effectiveness of not just the solution, but his overall strategy.
“One of the pillars of our infrastructure strategy was to build transparency across the organization. This comes from sharing metrics. With Tessian, we can show how many alerts were picked up and, each month, we can show the risk committee that we’re reducing the number of alerts.
Now, are they actually interested in our preventative controls? I don’t think so. But the whole point of the metrics program is to show how well (or badly) our strategy is performing.
Before, they would make their decision based on cost or how much risk they thought we were going to be mitigating. It was quite subjective. We’ve moved that now into something more data-based. We can actually say “Well, actually, we pay x per year and, as a result of that, we’re going in the right direction in terms of our risk mitigations.”
4. Tessian helps organizations stay compliant
Both Healthcare and Financial Services are highly regulated industries that are bound to several compliance standards beyond GDPR. That’s why, for Ted, protecting sensitive clinical data and ensuring “privacy and security by design” are both paramount.
“There’s a lot of data that we need to protect and prevent from getting outside of the four walls of ERT,” he said. “As an offshoot of GDPR in 2018, we had to classify all of the data, determine from a privacy perspective how to treat it from a sensitivity perspective, and then decide how to treat it from a security perspective.
Because it’s very easy to pull sensitive data and incur data loss on email, we needed a solution that would help us ensure data isn’t distributed where it shouldn’t go. That’s why we approached Tessian.”
For more information about compliance in Financial Services, check out this article: Ultimate Guide to Data Protection and Compliance in Financial Services.
“That’s where we really see the value with Tessian. It takes the burden off of people in my security team.”
Martyn Booth
Chief Information Security Officer (CISO) at Euromoney Institutional Investor
5. Tessian saves security teams time
While essential for compliance, classifying (and re-classifying) data, monitoring movement, investigating incidents, and generating reports all take a lot of time. That’s why 85% of IT leaders say rule-based DLP is admin-intensive.
With Tessian, security teams don’t have to do any of the above manually.
This is a big selling point for Martyn, who said, “That’s where we really see the value with Tessian. It takes the burden off of people in my security team.”
Tessian is powered by machine learning algorithms that have been trained on billions of data points. That means our solutions automatically understand what is and isn’t normal behavior for individual employees and can, therefore, detect and prevent threats before they turn into incidents or breaches. No rules required.
You can read more about our technology here.
6. Tessian gives security teams clear visibility of risks
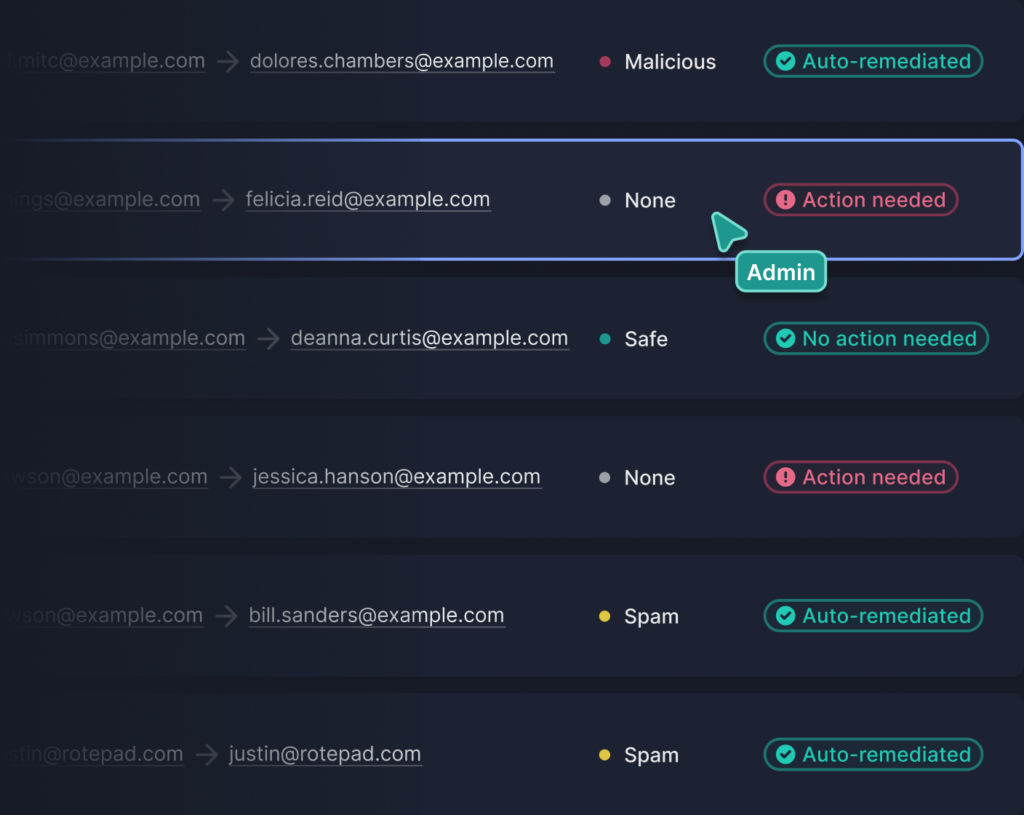
We’ve talked a lot about how Tessian detects and prevents risks. But for a solution to be really successful, it has to give security teams clear visibility of the risks in their organization.
Tessian’s Human Layer Security platform does both.
With Tessian Human Layer Security Intelligence, our customers can easily and automatically get detailed insights into employee’s actions.
For example, imagine that in a single week, Tessian detects 12 different employees attempting to send sensitive information to their personal email accounts. When warned that sending the email is against company policy, nine of the employees opted to not send the email. The other three went ahead.
Knowing this, security leaders can focus their efforts on the three that went ahead and offer additional, targeted training or, if necessary, they can escalate the incident to a line manager to issue a more formal warning.
This also helps predict future behavior.
For example, if Tessian flags that an employee has sent upwards of 20 attachments – including Intellectual Property that would be valuable to a competitor – to a recipient he or she has no previous email history with soon after being denied a raise or promotion, security teams could infer that the employee is resigning and taking company data with them.
And, to prevent any further data exfiltration attempts, they can create custom filters specifically for that user, including customized warning messages or a filter that automatically blocks future exfiltration attempts.
Before Tessian, this wasn’t possible for Martyn.
“Even if we suspected that an employee was going to go to a competitor and take data, we couldn’t check. We couldn’t see anything that was going up to the Cloud. It was all encrypted. The only way we would be able to see what people were emailing would be to actually go through individual emails to find ones that were problematic. We didn’t have time for that,” he said.
“You can’t take a 'big bang' approach to data privacy awareness training. To really see employees empowered, you have to constantly reinforce training.”
Ted Crawford
Chief Information Officer (CIO) at ERT
7. Tessian helps reinforce training and improve employee’s security reflexes with in-the-moment warnings
In the example above, three employees opted to send an email after being warned that doing so would be against company policy. But, what about the other nine? The warning message changed their behavior! It actually incentivized them to accurately mark emails as confidential or malicious if they were, in fact, confidential or malicious. This is really important.
“You can’t take a ‘big bang’ approach to data privacy awareness training. To really see employees empowered, you have to constantly reinforce training,” Ted said.
The bottom line: For training to be effective long-term, employees need to apply what they learn to real-world situations and be reminded of policies in-the-moment. Over time, this will help improve their security reflexes and help build a more positive security culture.
Henry Trevelyan Thomas, the host of the webinar and Tessian’s Head of Customer Success, summarized the benefits of this for both employees and security leaders, “This is a really productive way to help employees take accountability for how they handle data. It democratizes security and takes some of the weight off of the Chief Information Security Officer’s shoulders.”
Tessian can help prevent data exfiltration in your organization, too
Tessian turns an organization’s email data into its best defense against inbound and outbound email security threats.
Powered by machine learning, our Human Layer Security technology understands human behavior and relationships, enabling it to automatically detect and prevent anomalous and dangerous activity.
- Tessian Enforcer detects and prevents data exfiltration attempts
- Tessian Guardian detects and prevents misdirected emails
Importantly, Tessian’s technology automatically updates its understanding of human behavior and evolving relationships through continuous analysis and learning of the organization’s email network.
Oh, and it works silently in the background, meaning employees can do their jobs without security getting in the way.
Interested in learning more about how Tessian can help prevent accidental data loss and data exfiltration in your organization? You can read some of our customer stories here or book a demo.