Interviews With CISOs
- All Categories
- ...
-
 Interviews With CISOs
Interviews With CISOsWatch Again: Fwd: Thinking – The Intelligent Security Summit
-
 Interviews With CISOs, Podcast, Compliance
Interviews With CISOs, Podcast, ComplianceLola Obamehinti on What Good Security Awareness Training Looks Like
-
 Integrated Cloud Email Security, Interviews With CISOs
Integrated Cloud Email Security, Interviews With CISOsHot Takes: 8 Ways to Strengthen the CISO and CFO Relationship
-
 Interviews With CISOs
Interviews With CISOsAlmost Half of Chief Information Security Officers (CISOs) Have Missed A National Holiday Due to Work
-
 Interviews With CISOs
Interviews With CISOsQ&A with Karl Knowles, Global Head of Cyber at international law firm HFW
-
 Email DLP, Interviews With CISOs
Email DLP, Interviews With CISOsQ&A with Punit Rajpara, Head of IT and Business Systems at GoCardless
-
 Interviews With CISOs
Interviews With CISOsQ&A with Tim Fitzgerald, Chief Information Security Officer at ARM
-
 Interviews With CISOs, Podcast
Interviews With CISOs, PodcastQ&A with Ben Aung, Chief Risk Officer at SAGE
-
 Interviews With CISOs
Interviews With CISOsQ&A with Jerry Perullo, CISO at ICE
-
 Integrated Cloud Email Security, Interviews With CISOs, Advanced Email Threats
Integrated Cloud Email Security, Interviews With CISOs, Advanced Email ThreatsAll Cybersecurity 2022 Trend Articles Are BS, Here’s Why
-
 Interviews With CISOs
Interviews With CISOsCISOs, Here’s the Only Three Metrics That Matter to Your CEO
-
 Interviews With CISOs
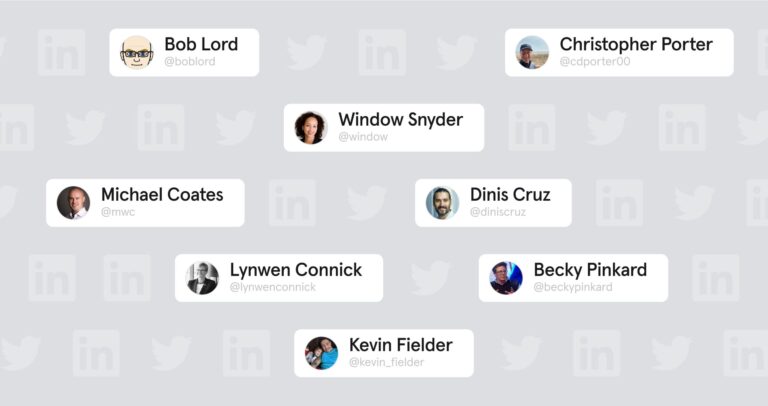
Interviews With CISOs12 CISOs to Connect With On LinkedIn and Twitter
-
 Interviews With CISOs
Interviews With CISOsRelationship 15: A Framework to Help Security Leaders Influence Change
-
 Integrated Cloud Email Security, Interviews With CISOs
Integrated Cloud Email Security, Interviews With CISOsRecap: Tessian Webinar, Can Automation Supercharge Your IT Team?
-
 Interviews With CISOs
Interviews With CISOsTessian Spotlight: Bridget Kenyon, Global Chief Information Security Officer at Thales eSecurity
-
 Interviews With CISOs
Interviews With CISOsTessian Spotlight: Helen Rabe, Global Chief Security Officer of Abcam
-
 Interviews With CISOs
Interviews With CISOsTessian Spotlight: Craig Hopkins, Chief Information Officer for the City of San Antonio
-
 Interviews With CISOs
Interviews With CISOsTessian Spotlight: Andrew Besford, former Deputy Director, Government Digital Service, UK Government
-
 Interviews With CISOs
Interviews With CISOsTessian Spotlight: Graham Thomson, CISO at Irwin Mitchell
-
 Interviews With CISOs
Interviews With CISOsTessian Spotlight: Sarat Muddu, IT Security Director at Kelley Drye
- 1
- 2







