Customer Stories
Read our latest Customer Stories, interviews and news. Learn how Tessian protects organisations in Financial Services, Legal, Technology and other markets.
- All Categories
- ...
-
 Customer Stories
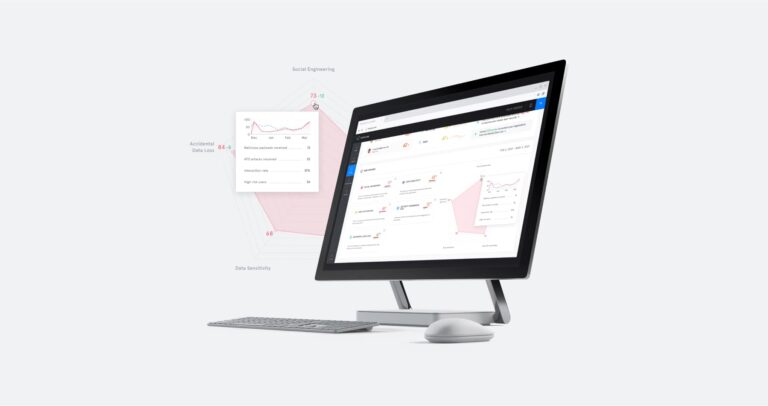
Customer StoriesPreventing Data Exfiltration at a FTSE 100 Tech Company
-
Integrated Cloud Email Security, Email DLP, Customer Stories
16 Ways to Get Buy-In For Cybersecurity Solutions
-
 Email DLP, Customer Stories
Email DLP, Customer StoriesCustomer Story: How Tessian Helped a Private Equity Firm Achieve Threat Visibility Through A Platform Approach
-
 Email DLP, Customer Stories
Email DLP, Customer StoriesCustomer Story: How Tessian Combines Data Loss Prevention With Education in Financial Services
-
 Customer Stories
Customer StoriesAdvanced Inbound and Outbound Threat Protection for an International Law Firm
-
 Integrated Cloud Email Security, Advanced Email Threats, Customer Stories
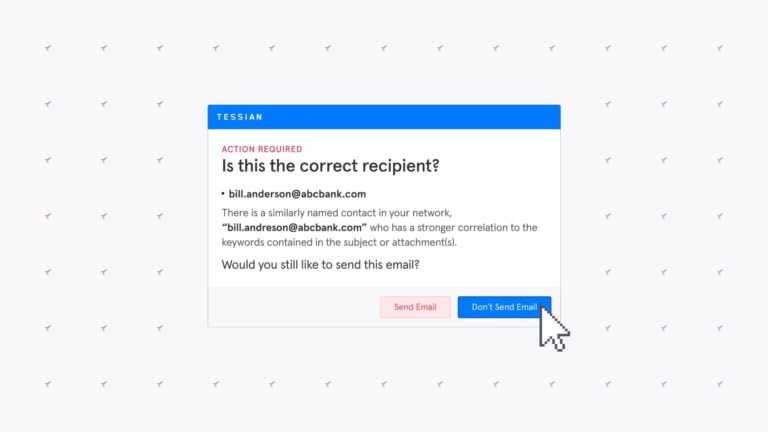
Integrated Cloud Email Security, Advanced Email Threats, Customer StoriesHow Tessian Reduced Click-Through Rates on Phishing Emails From 20% to Less Than 5%
-
 Customer Stories
Customer StoriesWhy Schroders Adopted Tessian 5 Years Ago, And How The Platform Has Evolved Since Then
-
 Customer Stories
Customer StoriesHow Tessian Gave GoCardless Better Control and Visibility of Their Email Threats
-
 Customer Stories
Customer StoriesHow Tessian Is Preventing Advanced Impersonation Attacks in Manufacturing
-
 Email DLP, Customer Stories
Email DLP, Customer StoriesWhy Metropolitan Gaming Chose Tessian as Their Complete Outbound Email Security Solution
-
 Integrated Cloud Email Security, Customer Stories
Integrated Cloud Email Security, Customer StoriesRecap: Tessian Webinar, How to Build a Security Culture in Today’s Working World
-
 Integrated Cloud Email Security, Customer Stories
Integrated Cloud Email Security, Customer StoriesRecap: Q&A With Chris Kovel, CTO, PJT Partners
-
Integrated Cloud Email Security, Email DLP, Advanced Email Threats, Insider Risks, Compliance, Customer Stories
18 Actionable Insights From Tessian Human Layer Security Summit
-
Integrated Cloud Email Security, Email DLP, Customer Stories
9 Questions That Will Help You Choose The Right Email Security Solution
-
 Integrated Cloud Email Security, Email DLP, Customer Stories
Integrated Cloud Email Security, Email DLP, Customer StoriesData Leakage and Exfiltration: 7 Problems Tessian Helps Solve
-
 Integrated Cloud Email Security, Email DLP, Advanced Email Threats, Customer Stories
Integrated Cloud Email Security, Email DLP, Advanced Email Threats, Customer Stories13 Things We Learned at Tessian Virtual Human Layer Security Summit
-
 Customer Stories
Customer StoriesKeeping Sensitive Client Data Safe
-
 Integrated Cloud Email Security, Customer Stories
Integrated Cloud Email Security, Customer StoriesCybersecurity Awareness Should Be People-Centric, Too
-
 Customer Stories
Customer StoriesMitigating the Risk of Data Exfiltration in a Regulated Industry
-
 Customer Stories
Customer StoriesStrengthening Security in Biotechnology







