Like Gandalf The Grey, it goes by many names.
Fast Company calls it the Great Reprioritization. LinkedIn prefers the Great Reshuffle, while Thrive Global opts for Great Re-evaluation. But whatever it’s called, it’s clearly a movement that’s broadened out from people quitting their jobs and moving to your competitors, to something much bigger around company culture, work/life balance, and job flexibility.
So what does this mean for your organization? How do you keep your data secure when your perimeter is over the horizon, your people are remotely distributed, and you’re facing threats that are increasing in both frequency and complexity?
What is the great re-evaluation?
The first wave of Great Resignation in 2021 saw an initial rush of people deciding they wanted a change, and quickly leaving their jobs. We covered the knock-on effects of keeping your data safe back then in this article.
And while much of those concerns are still valid, we’re now in a new space where other issues are starting to reveal themselves, too.
Those initial leavers were the “early adopters” who probably had itchy feet anyway, COVID was just the push they needed. But what about those who stayed?
Having weathered the storm for the last two years and seen that it’s showing no signs of abating, people are looking around for companies that offer better remuneration, flexibility, and an exciting mission. Things they’re (likely) sorely missing in their current companies.
As the CISO, those things might not be in your power to grant to the entire company. But as your company’s security leader, you own the security impact of when people leave, when their replacements arrive, as well as those who choose to stay.
Who’s leaving?
First off, let’s look at those who are (still) leaving. Resignation rates are highest among mid-career employees; that is those between 30 and 45 years old. And according to Harvard Business Review, the greatest churn was in Tech companies.
They’re often highly experienced at their role and unlike younger employees, don’t need a lot of training. What’s more, they’re not leaving to ‘drop out’ and start a lifestyle project or go traveling, they’re leaving for a better, more flexible package.
These are staff who ‘know where the bodies are buried’. They have a highly detailed knowledge of your organization and its processes, products, and customers. This group has the highest probability of attempting to exfiltrate sensitive data – IP, clients or other corporate information – from your organization.
But the problem isn’t limited to mid-career employees in the tech industry. The Verizon Data Breach Investigations Report found that 72% of staff take some company data with them when they move on, whether intentionally or not. They also found that 70% of intellectual property theft occurs within the 90 days before an employee’s resignation announcement.
Even worse, a whitepaper published by Osterman Research found that a further 28% of employees admitted to taking data created by others when they leave – cheeky! Things to look out for include fluctuations in email activity, accessing documents or files at unusual times such as evenings or weekends, and spikes in data transfers.
If you’ve disabled your USB ports, email remains one of the most popular conduits for exfiltration attempts, so securing that channel now – before they hand in their resignation – is critical.
Once that’s in place, you need a structured and effective offboarding process in conjunction with your People team to disable methods of data exfiltration. (There’s some great advice on designing that process as a whole over on Security Intelligence and on AT&T Business.)
Why high attrition is a threat to your data security
A data breach has a number of financial consequences. First and foremost, there’s the time it takes you to handle the incident. There’s potential compliance violations and regulatory fines, legal costs pursuing the ex-employee, and loss of reputation and competitive advantage that will affect your bottom line long-term.
The situation can be even worse when staff are let go as companies trim to stay afloat. One former credit union employee deleted 21GB of data after being fired, and one business collapsed entirely after an angry ex-employee deleted every single file.
Who’s arriving?
The good news – enthusiastic new staff are brought in to replace those who have left, so aren’t likely to exfiltrate any data. The bad news? They’re also vulnerable to external attacks, and have yet to get up to speed on your security processes and familiarize themselves with the company as a whole.
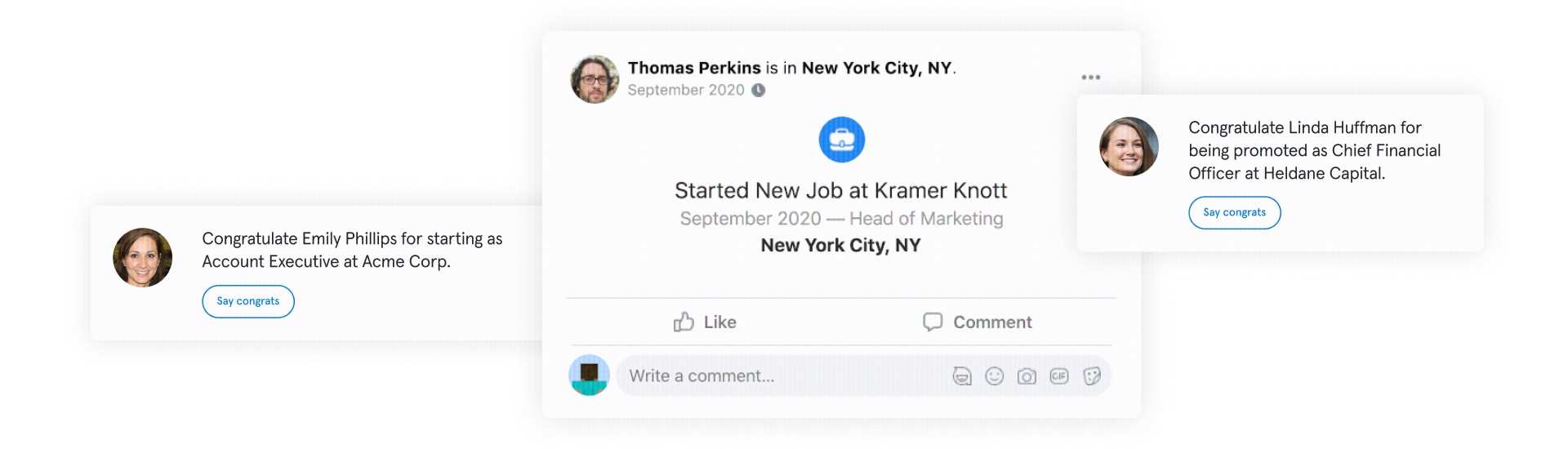
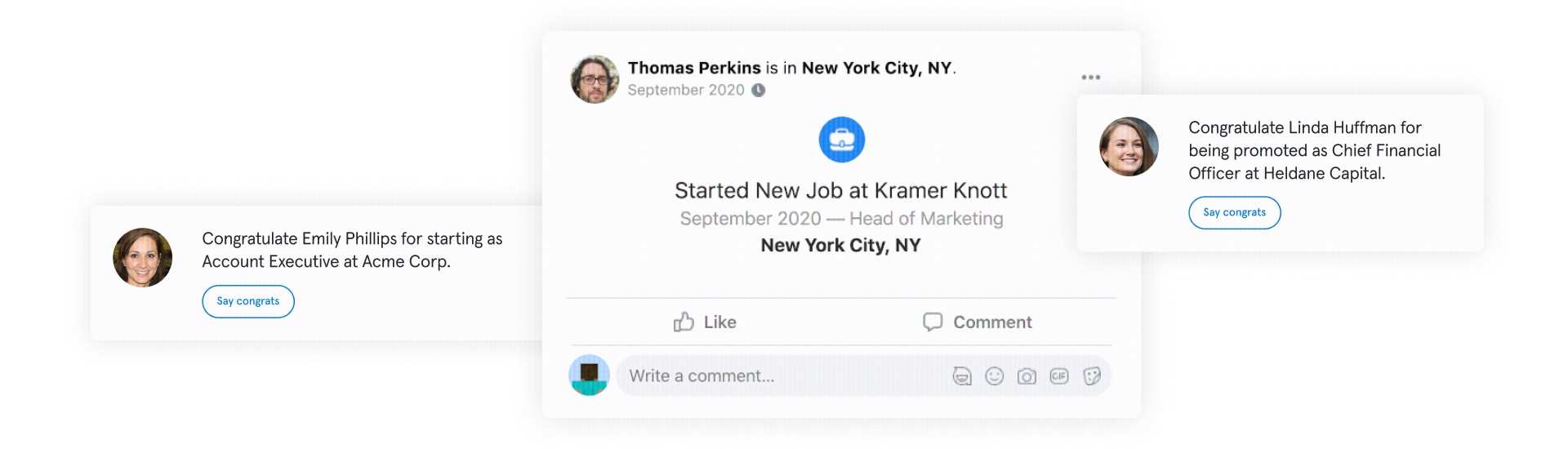
What’s more, they’ve probably announced their new role on social media. Our How to Hack a Human Report found that an overwhelming 93% of workers also update their job status on social media, while 36% share information about their job. Hackers know this, and do their research before hitting an organization with a spear phishing attack. Consequently, new starters are prime targets.
But it’s not just role replacement staff, it’s entirely new staff too. After all, the pandemic has been very good for certain industries (infomation security for example) and some businesses are growing off the back of this and expanding their teams.
Who’s staying?
When a team changes, there’s always disruption of some sort, and that problem is only exacerbated in today’s remote world. However, that disruption can also be an opportunity to refresh and remind people what a good security culture looks like and correct any bad habits that might have formed during remote working.
This is important as our ‘Back to Work’ research report found the following alarming statistics:
- 56% of IT leaders believe employees have picked up bad cybersecurity behaviors since working from home
- 40% of employees plan to bring their personal device into the office to work on
- 69% of IT leaders think that ransomware attacks will be a greater concern in a hybrid workplace
- 27% of workers are afraid to tell IT they’ve made a security mistake
Hybrid is here to stay – act accordingly
Why the office is done
The halcyon days of on prem servers and a load of desktop PCs all protected by a shiny new Secure Email Gateway (SEG) are long gone. And now, the office that once housed them is on the way out, too. According to one study, 79% of the C-suite say they will permit their staff to split their time between corporate offices and remote working, if their job allows for it.
There was the assumption in late 2021 that, once a vaccine was developed and staff afforded some sort of protection, things would soon return to normal – or at least something like it. Omicron has blown that notion to smithereens. And as this article suggests, maybe it’s time to admit defeat.
Remote working isn’t going anywhere anytime soon, and staff are still subject to the same distractions and security threats they were in March 2020.
The enemy here is complacency: bad habits as much as bad actors. People are once again distracted, angry, and anxious. Here’s some quick tips to help remind the team about good security practices (see more here)
- Use company-approved cloud or VPN services to access work documents instead of emailing sensitive information to your personal email accounts.
- Don’t download new software or tools without consulting your IT team.
- Keep your software and operating systems up-to-date.
- Always lock your laptop and keep all of your devices password-protected.
- If you make a mistake and find yourself alarmed or fearful, it’s important to stop, think, and get someone else involved to support you.
Look after yourself
Like an airplane oxygen mask, you can’t look after others until you’ve looked after yourself first. It’s been a tough few years and CISOs are burnt out, really burnt out. Our Lost Hours report found that CISOs, on average, worked 11 hours a week in unpaid overtime, and that 25% of CISOs spend 9-12 hours investigating and remediating each threat caused by human error. What’s more, the average time a CISO is in post is as little as 26 months.
A commissioned study conducted by Forrester Consulting on behalf of Tessian identified that organizations spend up to 600 hours per month resolving employee-related email security incidents. That is not healthy and it’s not sustainable, for either staff or the business.
And your team
As our 2022 trends post highlighted, hiring and keeping a diverse team will be one of your biggest priorities… and challenges. After all, at the end of 2021 there were nearly 500,000 unfilled cybersecurity roles in the US. The Department for Homeland Security was looking to hire 1800 but the end of 2021 alone
Dealing with the rising security risks of the Great Re-evaluation needs a great team backed up by great tools that streamline defenses against phishing attacks and data exfiltration. That’s where we come in. So if you need some help we’d love to talk.
How does Tessian prevent data exfiltration attempts?
Prevent unauthorized emails
Whether it’s an employee sending sensitive information to less secure, personal accounts or a bad leaver maliciously exfiltrating data, Tessian automatically prevents data exfiltration over email.
Learn more
Deeply understand your risk
Whether careless, negligent, or malicious, insider threats are difficult to combat and even harder to detect. But with Tessian, you can quickly find and report the key areas of insider risk, use insights to predict future behavior, and take remedial action to prevent exfiltrations attempts.
Learn more
In-the-moment educational warnings
Tessian warnings act as in-the-moment training for employees, continuously educating them about treats, reinforcing your policies, and nudging them toward safe email behavior. Automatically build individualized policies at scale to reduce high-risk email use and track trends in unsafe activity over time.
Learn more
Andrew Webb
Senior Content Manager