Security and risk management teams are focused on detecting, investigating, and responding to cyber security incidents. Given the high number of security tools deployed in the environment of a typical organization, reviewing security events that could be actual incidents requires dedicated FTE resources and time. This creates two challenges.
1: A delayed response time in triaging security events and finding incidents can also result in worsening the fallout from a breach, thereby elevating the level of risk.
2: Security teams find it increasingly time consuming to handle this volume of events, potentially resulting in analyst burn out, loss of retention and a reduced quality in event investigation.
Improving the efficiency for event triage is essential to help security and risk leaders speed up investigations and remediate incidents.
Working Smarter, Not Harder
A recent Tessian commissioned study by The Ponemon Institute found that “it can take an average of 72 hours to detect and remediate a data loss and exfiltration incident caused by a malicious insider on email and an average of almost 48 hours to detect and remediate an incident caused by employees’ negligence or error on email.”
This is why Tessian has focused on making the investigation process more efficient for our users with a new event triage workflow.
Enhanced security event management
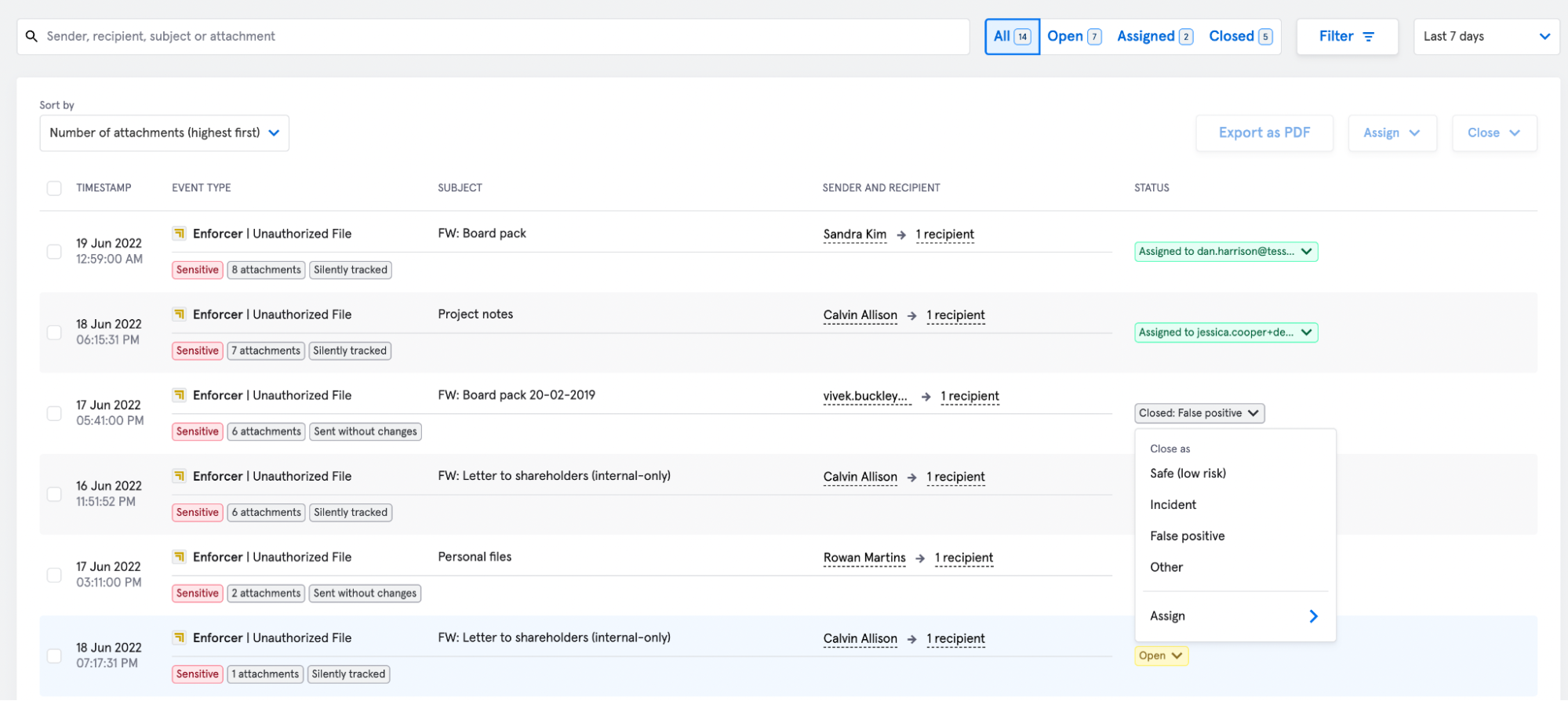
Tessian has improved security efficiency for customers through enhanced event triage in the Tessian Portal for all of our data loss modules, Guardian, Enforcer and Architect. Our latest feature update includes:
- The ability for security admins to view the full email body and attachment for a flagged email.
- The ability for users to label events within its workflow status. The event statuses can be marked as Open, Incident, Safe, False Positive, and Other.
These capabilities enable Tessian users to get more context on a security event and easily collaborate with team members, leading to a more efficient end-to-end investigation process. These enhanced capabilities extend across M365 and GSuite mailboxes.
Making the SOC more efficient
The new event triage enhancements demonstrated below, enables security analysts to view the email body and to more effectively triage the security events. The advantage this brings to security teams is being able to immediately access the event content, rather than requesting the email content often from a separate team. This speeds up the investigation workflow and reduces the dependency security teams have on other parts of the organization. Further enhancements include being able to assign security events to team members and labeling the event with its workflow status (open, incident, safe, false positive, other).
Portal View of Security Event - Email Body View
These new feature enhancements will enable:
• The ability to complete end-to-end investigations all within the Tessian Portal resulting in a more efficient response to security threats.
• Improved SecOps efficiency in dealing with actual events vs. false positives.
• The ability to more easily collaborate with team members through the assignment of events, helping teams remain focused on what matters most.
• Insight into the outcome of data loss events through event status tagging, helping the CISO gauge risk using real data and helping to measure Tessian’s Return on Investment
Portal View of Email Security Events
A note on privacy
The ability for security teams to view the full body of emails and their attachments may pose a privacy concern to customers. In recognition of this, we have built in some privacy guard rails which customers can use to control and monitor data access. Only Tessian users who have the necessary permissions to view the full email body and attachments will be able to do so. In addition, whenever a user requests to view the email’s full body and attachment, an audit event will be created which can be viewed within the Tessian portal.
To see how the Tessian Intelligent Cloud Email Security platform prevents ransomware attacks, and protects against DLP, watch a product overview video or book a demo.
For the latest cybersecurity news and articles, sign up for our newsletter, and follow us on Twitter and LinkedIn
Dan Harrison
Product Manager