After many years working to secure the networks, computers, applications and connected devices that power our world, I joined Tessian a little over 90 days ago to help them in their journey to eliminate human influenced cyber attacks, accidents, and insider threats from the enterprise.
So why Tessian and why now?
Targeted email attacks such as business email compromise (BEC), spear phishing, account takeover, and ransomware continue to be the number one and most damaging human-influenced cyber threats to businesses.
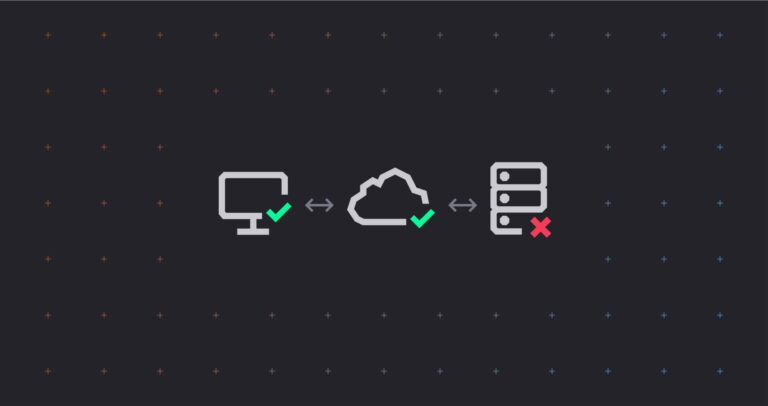
As businesses move to cloud-based email services like Microsoft 356 and Google Workspace, they are looking for email security solutions that can be combined with the capabilities of these platforms. A new market space – Integrated Cloud Email Security (ICES) – is emerging to fill this need.
I believe the evolution of ICES will follow a pattern similar to that of the emergence of Endpoint Detection and Response (EDR) in endpoint protection space, and Cyber Asset Attack Surface Management (CAASM) in asset management space: legacy solutions pivoting into the new market and forward thinking new companies looking to disrupt the status quo.
Tessian has the forward thinking necessary to become one of the visionaries in this space. I am excited to join Tessian to help accelerate their execution to become the leader. The journey is just starting to be interesting!
Moreover, Tessian is not playing a “finite game” (good news for you Simon Sinek fans!). Our vision is to secure the human layer. This vision is beyond just email security, and one that I can get behind.
Just like physical security, cybersecurity has been taking an adversarial approach to protecting the networks and computers humans engage in the course of doing day-to-day business. Over the past several decades we have built solutions that protect network perimeters and detect and respond to anomalies in machines running applications and software.
Today, employees in an organization use multiple interfaces; email, messaging, shared drives, and documents, to access and work with (sensitive) data. Many solutions put rules and boundaries around such interactions without learning from and adapting to the changing nature of them; they are not only insufficient but also restrictive.
Tessian aspires to protect every business’ mission while empowering their people to do their best work. This is not an end goal but a shared purpose.
Lastly, no company aspiring to secure the human layer could be true to itself if it wasn’t human-first and customer-centric. These are part of Tessian’s core values, and I look forward to building a company that exemplifies these values everyday and learns from the industry experts, our partners, and of course our customers.
It has been a whirlwind 90-days so far! If you are interested in knowing more about Tessian, or would like to work with us, or you are an expert with an idea to pitch, reach out to me. I would be happy to hear from you, and our open roles are here.
Gün Akkor
VP of Engineering