Compliance
Read our latest articles, tips and news on Compliance including GDPR, CCPA and other industry-specific regulations and compliance requirements.
- All Categories
- ...
-
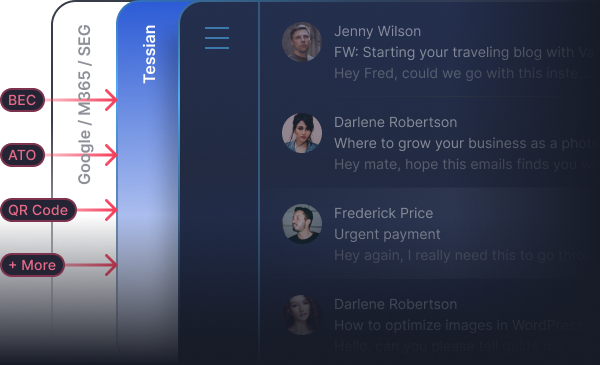
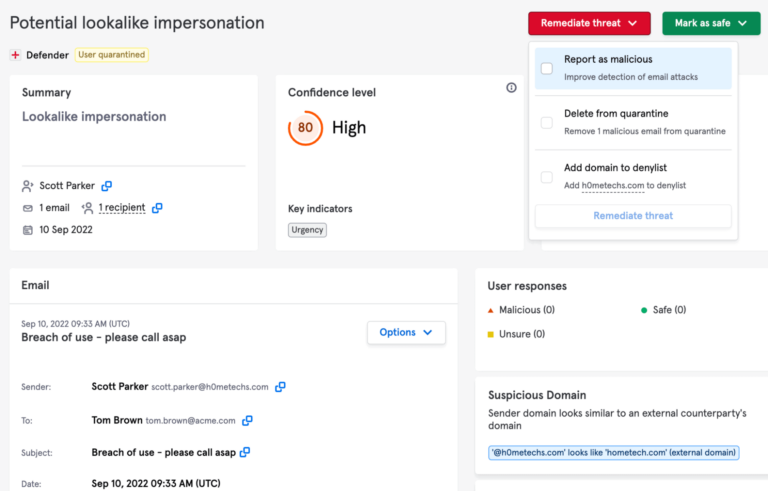
 Integrated Cloud Email Security, Compliance
Integrated Cloud Email Security, Compliance10 Reasons Why CEOs Should Care About Cybersecurity
-
Compliance
CCPA FAQs: Your Guide to California’s New Privacy Law
-
 Compliance
Compliance6 Reasons to Download The CEO’s Guide to Data Protection and Compliance
-
 Email DLP, Insider Risks, Compliance
Email DLP, Insider Risks, ComplianceA Beginner’s Guide to Cybersecurity Frameworks
-
 Advanced Email Threats, Insider Risks, Compliance
Advanced Email Threats, Insider Risks, ComplianceSeptember Cybersecurity News Roundup
-
 Email DLP, Advanced Email Threats, Insider Risks, Compliance
Email DLP, Advanced Email Threats, Insider Risks, ComplianceCompliance in the Legal Sector: Laws & How to Comply
-
Integrated Cloud Email Security, Email DLP, Advanced Email Threats, Insider Risks, Compliance, Customer Stories
18 Actionable Insights From Tessian Human Layer Security Summit
-
 Email DLP, Compliance
Email DLP, ComplianceUltimate Guide to The POPIA – South Africa’s Privacy Law
-
 Compliance
ComplianceSecurity vs. Compliance: What’s The Difference?
-
Email DLP, Advanced Email Threats, Insider Risks, Compliance
August Cybersecurity News Roundup
-
Compliance
Ultimate Guide to Data Protection and Compliance in Financial Services
-
Email DLP, Advanced Email Threats, Compliance
July Cybersecurity News Roundup
-
Compliance
US Data Privacy Laws 2020: What Security Leaders Need to Know
-
 Integrated Cloud Email Security, Compliance
Integrated Cloud Email Security, ComplianceTwo Years Later: 3 Ways GDPR Has Affected Cybersecurity
-
Email DLP, Compliance
5 Things Every CISO Should Know About CCPA’s Impact on Their InfoSec Programs
-
 Compliance
ComplianceThe Impact of POPI on Your Organization
-
 Compliance
ComplianceThe California Consumer Privacy Act (CCPA) Could Set a New Standard for Privacy and Data Security in the US
-
 Compliance
ComplianceThe Week the ICO Bared Its Teeth
-
 Compliance
ComplianceInfosec19: A year of GDPR
-
 Compliance
ComplianceGDPR’s Anniversary: What We’ve Learned and What’s Next
- 1
- 2







