Amazon, UPS, DHL, FedEx, USPS, Royal Mail – logistics delivery is a huge part of our lives. Amazon is said to ship 1.6m parcels a day and DHL delivers over 1.5 billion parcels per year.
Of course all these parcels make this sector a prime theatre for bad actors to operate in. Why? Think about the process for ordering a package. You enter card details, your email address, and other Personally Identifiable Information (PII) like your home address. And, as we all know, pretty much all of us use logistic delivery services at some point.
In fact, according to Tessian research, nearly half (47%) of people say they shopped online more in the last year than the year prior. It’s no wonder delivery impersonation attacks are among the most common types of cyberattacks targeting people today.
What’s more, delivery impersonation scammers are using increasingly complex and hard-to-spot tactics to carry out their attacks.This article will explain what a delivery impersonation attack is and provide helpful guidance on how you can help yourself and your organization avoid falling victim to this type of scam.
What is a delivery impersonation attack?
First things first: what is a delivery impersonation attack?
A delivery impersonation attack is a type of phishing where the attacker impersonates a delivery company.
The scam involves sending a fraudulent SMS or email to a consumer, telling them that they have missed a delivery. The message contains a link that, when followed, leads to a website operated by the scammers.
When the target visits the fraudulent website, they are duped into revealing personal information, such as their login credentials, contact details, or payment information.
How common are delivery impersonation attacks?
It’s no exaggeration to say that delivery impersonation attacks are an endemic and widespread security threat.Delivery impersonation attacks occur year-round, but spike around the same periods each year, typically when consumers are making a lot of online orders—most notably around Black Friday.
In Q3 2020, Tessian detected a significant spike in fraudulent email activity in the run-up to Black Friday, as cybercriminals attempted to exploit the increase in online deliveries. More recent Tessian research reveals that around 20% of US consumers and 33% of UK consumers have received a delivery impersonation email or SMS so far in 2021.
This increase in delivery impersonation is part of a general surge in phishing that has occurred since the start of the pandemic.In October 2021, research from Ofcom revealed that 82% of UK adults received a suspicious text or email in the preceding three months. The situation has gotten so bad that the UK Government announced it was relaunching its Joint Fraud Taskforce in response.
Telltale signs of a delivery impersonation attack
Now we’ve explained what a delivery impersonation attack is, let’s consider what such an attack looks like.
As explained, a delivery impersonation message will always contain a link. The aim of the attack is to get you to click or tap the link and give up your personal information.
Therefore, it’s crucial that you carefully inspect any link contained in a text or email to determine whether it is malicious.
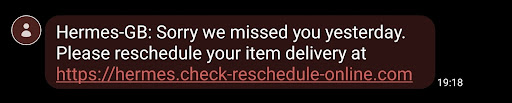
Here’s an example:
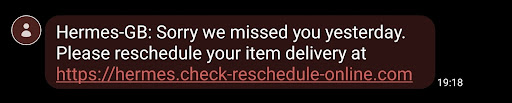
The phishing link contained in this delivery impersonation message points to a site that is operated by scammers, rather than the delivery company Hermes. But how can you tell whether a URL is malicious?
Well, it’s not always obvious. While some URLs are blatantly fraudulent, fraudsters have come up with ingenious ways of creating links that really look right. Here are some examples of different URL impersonation techniques.
Root domain impersonation
The “root domain” is the part of the URL that appears before the “top-level domain”. So, in “www.amazon.com”, the root domain is “amazon”, and the top-level domain is “.com”.
Amazon owns the root domain “amazon”, so fraudsters can’t simply set up their own phishing sites under that domain. But they can create domains that look like “amazon.com” to fool people into clicking their phishing links.
One common root domain impersonation tactic is to use numbers instead of letters. So, swap the “o” in “amazon” with a zero, and you have “amaz0n.com”. At first glance, an undiscerning target might mistake this for Amazon’s actual website.
However, root domain impersonation is increasingly uncommon as this trick is relatively easy to spot. Also, major brands tend to buy up similar-looking domains to prevent cybercriminals from acquiring them.
Tessian research reveals that only 20% of top couriers have configured their website’s DMARC policies to the strictest settings. This means fraudsters can use tactics like email spoofing to convincingly imitate these sites via fraudulent emails.
Subdomain impersonation
One highly persuasive impersonation technique is to include the impersonated company’s name in the subdomain of a URL operated by the cybercriminals. The subdomain is the part of a URL that appears before the root domain of a website.
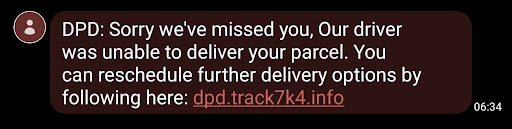
Here’s an example of a delivery impersonation attack message impersonating delivery company DPD:
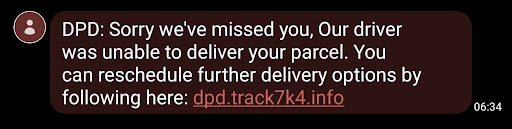
The first part of this link is “dpd”, and so it may appear to lead to DPD’s website. However, the root domain—the website operated by the fraudsters—comes after “dpd”. It’s “track7k4”. So, if you receive a delivery message that looks real at first glance, take special care to check whether the root domain is as authentic-looking as the subdomain.
Top-level domain impersonation
Attackers can also impersonate the top-level domain of a URL to make it appear authentic. The top-level domain appears last in a URL. Common examples include “.com”, “.net”, and “.co.uk”.
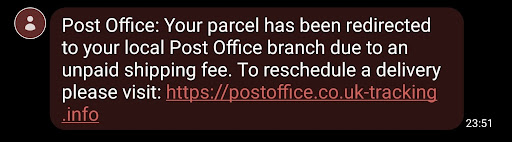
Here’s an example:
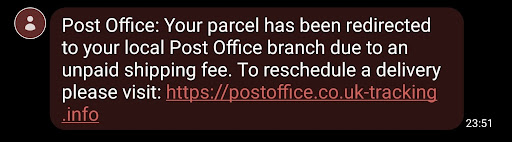
In this delivery impersonation message, the link points to a URL that might seem authentic at first glance. Visiting “postoffice.co.uk” would take you to the Post Office website. But this URL doesn’t actually lead to “postoffice.co.uk”—the top-level domain is “co.uk-tracking.info”, not “.co.uk”. Note that the words “uk” and “tracking.info” are separated by a hyphen rather than a forward-slash, meaning that both words are part of the top-level domain.
Protecting employees from delivery impersonation attacks
As noted, delivery impersonation attacks mainly target consumers. But they can be a problem for businesses too—particularly in the age of “bring-your-own-device” and remote working.So how can you protect your organization from delivery impersonation attacks?
Unfortunately, there is little you can do to stop employees from receiving delivery impersonation attacks via SMS. Android and iOS have some basic filtering and notification functions, but these often fall short and allow delivery impersonation attacks to reach people’s mobiles.
Therefore, incorporating information about delivery impersonation attacks into your company’s security training program is essential. When it comes to preventing delivery impersonation attacks via email, there is a viable solution.
Tessian Defender uses machine learning, anomaly detection, behavioral analysis, and natural language processing to detect even the most subtle signs of email impersonation and phishing.
Here’s how it works:
- Tessian’s machine learning algorithms analyze your company’s email data, learning each employee’s usual communication patterns and mapping their trusted email relationships inside and outside of your organization.
- Tessian inspects both the content and metadata of inbound emails for signals suggesting email impersonation or other phishing attacks. Such content might include suspicious payloads, geophysical locations, IP addresses, email clients, or sending patterns.
- Once it detects a threat, Tessian alerts employees that an email might be unsafe, explaining the threat in easy-to-understand language.
Click here to learn more about how Tessian Defender protects your team from email impersonation and other cybersecurity attacks. You can also explore our customer stories to see how they’re using Tessian Defender to protect their people on email and prevent social engineering attacks like phishing.
Andrew Webb
Senior Content Manager