We’re back with another roundup of the biggest stories in cybersecurity in November 2020.
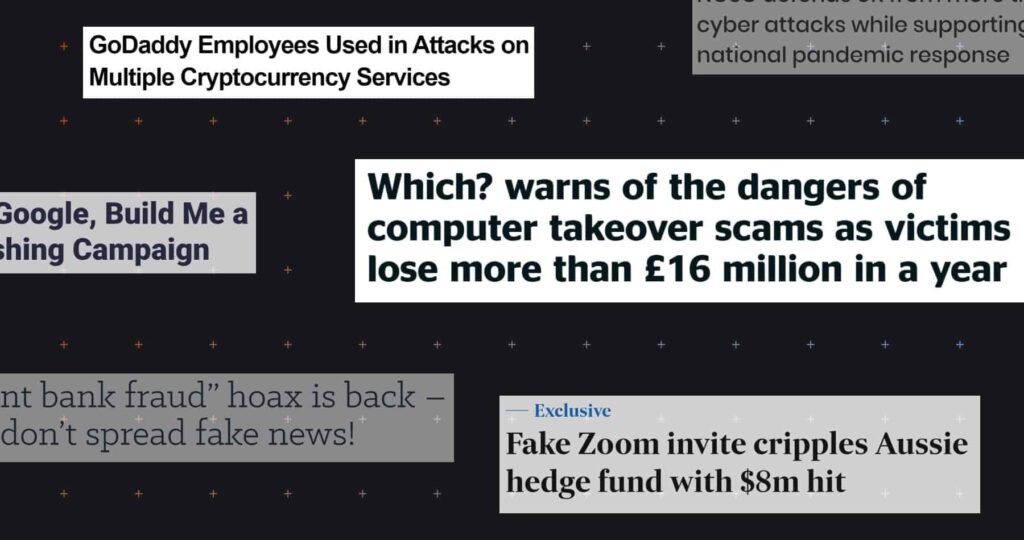
With phishing, hacking, and ransomware continuing to surge worldwide, there was a lot of news to choose from. We’ve selected stories representing the latest trends in cyberattacks — and demonstrating the myriad ways that cybercrime impacts businesses and consumers.
UK Hit By Record Number of Serious Cyberattacks
The UK’s National Cyber Security Centre (NCSC) published its 2020 annual review on November 3. The report revealed that the NCSC had defended the UK against a record-breaking 723 cyber incidents in the past year.
The data covers the period between September 1, 2019 and August 31, 2020 and reveals a 20.1% increase in cyber incidents compared to the previous three-year average (602 cyber incidents).
So what explains this surge in cybercrime? The NCSC chalks the increase in numbers up to its proactive approach in identifying and mitigating threats, together with tips from its “extensive network of partners” and public reports.
But there’s another reason: cybercriminals’ exploitation of the COVID-19 pandemic. The NCSC’s Suspicious Email Reporting Service received an incredible 2.3 million reports in its first four months of operation, leading to the removal of 166,710 phishing URLs.
In fact, phishing takes up a lot of space in the NCSC’s report, which highlights:
- A spate of spear phishing attacks targeting pharmaceutical companies
- An “explosion” in fake ads sent via phishing emails
- A rise in the percentage of businesses experiencing phishing attacks — from 72% in 2017 to 86% in 2020
Want to know more about how widespread phishing has become? Read our must-know phishing statistics.
Amazon Customers Targeted By Vishing Attacks
Our October roundup reported an increase in Amazon-related phishing scams around Prime Day. On November 7, the Guardian revealed another Amazon scam: Amazon Prime customers are being targeted in vishing (voice phishing) attacks.
Victims received calls from scammers impersonating “Amazon Prime Security” employees, who advised them that their accounts had been used to make suspicious payments.
Consumer group Which? described how one Amazon Prime customer was persuaded during a vishing call to install remote-access software on her device. The scammers then accessed her bank account and stole £6,900 (over $9,200).
UK cybercrime reporting agency Action Fraud said it had received 14,893 reports of similar “computer software service fraud” incidents over the past 12 months, resulting in losses of over £16 million ($21.3 million).
Vishing attacks are a massive problem for businesses as well as consumers. Read our guidance to find out more about defending against vishing attacks.
WhatsApp Hoax Spreads False Phishing Claim
On November 11, Naked Security reported a smishing (SMS phishing) scam that is, sadly, pretty unremarkable in the current climate. Victims received a text alerting them to an “unpaid phone bill,” and redirecting them to a fake O2 network credential-phishing login page.
What’s more unusual about this widespread smishing attack is the rumors surrounding it. According to Action Fraud, WhatsApp-based “fake news” proliferated in the days following the attack, spreading confusion among consumers.
The WhatsApp message, which referenced the City of London Police Fraud agency, claimed that the smishing attack was an “extremely sophisticated scam,” whereby attackers could drain money from victims’ accounts as a result of them merely “touching” the fraudulent text message.
This type of disinformation serves as another attack vector for cybercriminals. It can undermine the efforts of legitimate cybersecurity authorities. Repeated hoaxes of this kind could, ultimately, lead to reduced vigilance among the targets of cybercrime.
Credential phishing is a serious issue in itself — there’s no need to exaggerate the threat via phony WhatsApp chain messages. Read more about credential phishing here.
Fintech Platform Attacks Unwittingly Facilitated by GoDaddy Staff
Cryptocurrency trading platform Liquid reported on November 13 that its domain registrar, GoDaddy, had “incorrectly transferred control of (Liquid’s) account and domain to a malicious actor,” allowing the attacker to take control of internal email accounts.
The attack resulted in the theft of users’ email addresses, names, physical addresses, and encrypted passwords. Worse still, ID cards, selfies, and proof of address documents — collected as part of the site’s “Know Your Customer” requirements — may also have been compromised.
But GoDaddy’s problems don’t end there. Just five days later, crypto-mining service NiceHash revealed that its domain had been subject to “unauthorized access” owing to “technical issues” at GoDaddy. While NiceHash reported that user data was likely safe, its domain was unavailable for some time.
GoDaddy didn’t disclose details of the attacks, but Krebs on Security revealed in March that GoDaddy staff had been subject to a vishing attack that had compromised fintech website Escrow.com.
Whatever the specifics, it seems GoDaddy has suffered multiple social engineering attacks in the past year. Read our six real-world examples of social engineering attacks to learn how to avoid such problems.
Around 28 Million Texans’ Driver’s Licenses Compromised
Fox 26 Houston reported on November 18 that hackers had stolen nearly 28 million driver’s licenses registered in Texas. Driver’s license details are highly valuable to cybercriminals, who can sell them on the dark web or use them to commit identity fraud.
The attack has been blamed on weak security protocols, with data being “inadvertently” held in unsecured storage by service provider Vertafore. In addition to driver’s license numbers, names, birthdates, addresses, and vehicle registration details were also stolen.
The breach took place between March and August and affected drivers who had received their license before February 2019. Vertafore is offering victims one year of free credit monitoring.
More and more US states are introducing tough new data breach notification and privacy laws. Read our guidance on US privacy laws for business leaders to find out more.
Google Products “Weaponized” for Phishing Attacks
Research from Armorblox, published November 19, revealed how popular Google products, including Docs, Forms, and Firebase, have been exploited by cybercriminals and used to “defraud individuals and organizations of money and sensitive data.”
Why are hackers weaponizing Google products? Well, they’re typically open-source and easily-adapted. And because Google is ubiquitous and legitimate, Google-associated URLs are rarely blocked by firewalls or security software.
Examples of Google-based phishing attacks uncovered by the investigation include:
- A Google Form used to impersonate an American Express account-recovery page
- A fake email login page hosted on mobile API Google Firebase
- A Google Doc used as a fake payslip for a payroll diversion scam
Blocking your employees from accessing Google products and URLs would be undesirable and impractical. The only realistic way to avoid Google-exploit phishing scams is with effective email security software.
Tessian Defender uses AI-driven technology to detect suspicious activity in your employees’ inboxes automatically. Click here to find out how Tessian helps defend against phishing and other social engineering attacks.
Hedge Fund Forced to Close After $8 Million Phishing Attack
On November 22, the Australian Financial Review revealed how hedge fund Levitas Capital was defrauded for nearly $8.7 million following a phishing attack.
The attacker sent a fake Zoom invite link to one of the hedge fund’s co-founders. When they opened the Zoom link, malware was installed on their device. This allowed the attackers access to the fund’s corporate email account.
Using Levitas Capital’s email account, the hacker launched a Business Email Compromise (BEC) attack, sending fraudulent invoices to the fund’s administrators and trustees. The attack was discovered in late September after an examination of the fund’s online banking records.
All but $800,000 of the $8.7 million stolen was recovered before payments cleared. But the damage was done — following the attack, the fund lost its biggest client and was forced to close.
This case shows how devastating phishing attacks can be — even when the direct losses are mitigated. To find out more, read our articles on wire transfer phishing and Business Email Compromise (BEC) attacks.
South Korean Retailer Closes 23 Stores After Ransomware Attack
South Korean fashion conglomerate E-Land group announced that it was closing 23 of its 50 stores following a ransomware attack, according to a November 22 report from news agency Yonhap.
E-Land reportedly had to temporarily shut down part of its corporate network to contain the attack, meaning that nearly half of its NC Department Store and NewCore Outlet branches could not operate.
A company spokesperson confirmed that the attack had targeted E-Land’s headquarters. It is unclear whether E-Land group chose to pay the ransom or whether files or data were exfiltrated as part of the attack.
Ransomware continues to ravage the global economy. Last month we reported that US businesses could be breaching international sanctions rules if they attempt to salvage their files by paying a ransom. To help defend your business against ransomware and other cyberattacks, read our guide to choosing the right email security software.