Email DLP
- All Categories
- ...
-
 Integrated Cloud Email Security, Email DLP
Integrated Cloud Email Security, Email DLPWhat is Email DLP? Overview of DLP on Email
-
 Email DLP, Advanced Email Threats, Insider Risks
Email DLP, Advanced Email Threats, Insider RisksMergers and Acquisitions: Why Email Security Must Be a Priority
-
 Integrated Cloud Email Security, Email DLP, Advanced Email Threats, Compliance
Integrated Cloud Email Security, Email DLP, Advanced Email Threats, Compliance7 Ways CFOs Can (And Should) Support Cybersecurity
-
 Email DLP, Remote Working, Advanced Email Threats, Insider Risks
Email DLP, Remote Working, Advanced Email Threats, Insider RisksHow to Keep Your Data Safe in The Great Resignation
-
 Integrated Cloud Email Security, Email DLP, Insider Risks
Integrated Cloud Email Security, Email DLP, Insider RisksWhat is an Insider Threat? Insider Threat Definition, Examples, and Solutions
-
 Integrated Cloud Email Security, Email DLP, Compliance
Integrated Cloud Email Security, Email DLP, ComplianceAt a Glance: Data Loss Prevention in Healthcare
-
Integrated Cloud Email Security, Email DLP, Insider Risks, Compliance
The State of Data Loss Prevention in the Financial Services Sector
-
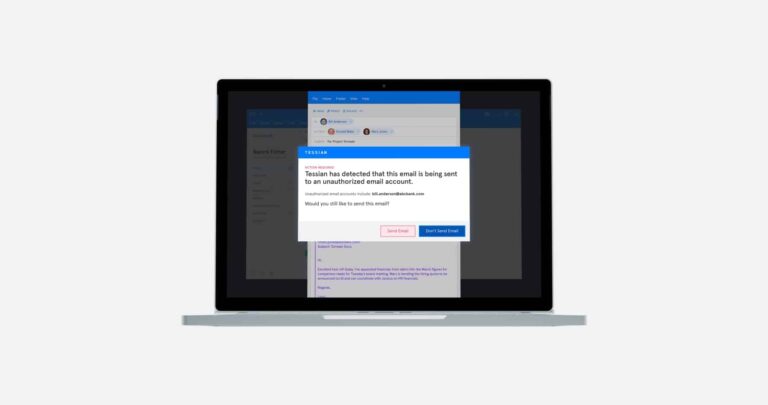
 Email DLP
Email DLPUnauthorized Emails: The Risks of Sending Data to Your Personal Email Accounts
-
 Email DLP
Email DLP7 Tips for SOC Teams Using Splunk
-
 Integrated Cloud Email Security, Email DLP, Insider Risks
Integrated Cloud Email Security, Email DLP, Insider Risks11 Examples of Data Breaches Caused By Misdirected Emails
-
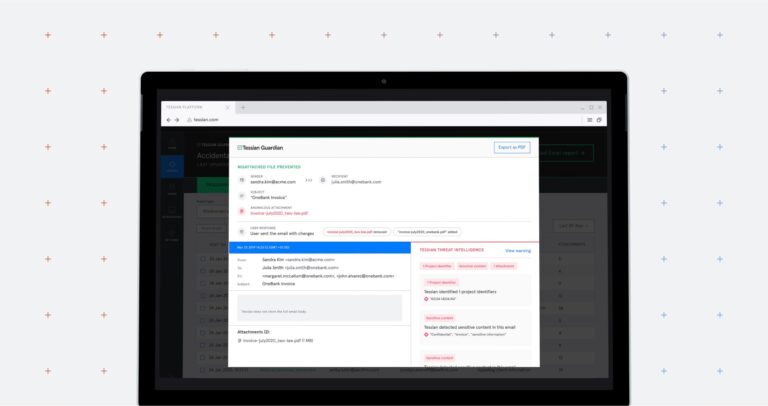 Integrated Cloud Email Security, Email DLP
Integrated Cloud Email Security, Email DLPIndustry-First Product: Tessian Now Prevents Misattached Files on Email
-
 Email DLP, Insider Risks
Email DLP, Insider Risks12 Examples of Data Exfiltration
-
 Email DLP, Customer Stories
Email DLP, Customer StoriesWhy Metropolitan Gaming Chose Tessian as Their Complete Outbound Email Security Solution
-
Integrated Cloud Email Security, Email DLP, Advanced Email Threats, Insider Risks
Worst Email Mistakes at Work and How to Fix Them
-
 Email DLP, Advanced Email Threats
Email DLP, Advanced Email ThreatsDecember Cybersecurity News Roundup
-
 Email DLP, Insider Risks
Email DLP, Insider Risks2020 in Review: Top 17 Insights From Tessian Research
-
 Email DLP
Email DLPEmail Security: Best Practices and Tools to Lock Down Email
-
 Integrated Cloud Email Security, Email DLP, Advanced Email Threats, Insider Risks
Integrated Cloud Email Security, Email DLP, Advanced Email Threats, Insider RisksOctober Cybersecurity News Roundup
-
 Email DLP, Integrated Cloud Email Security, Advanced Email Threats, Insider Risks
Email DLP, Integrated Cloud Email Security, Advanced Email Threats, Insider RisksTessian Included as a Cloud Email Security Supplement Solution in Gartner’s 2020 Market Guide for Email Security
-
 Email DLP, Insider Risks, Compliance
Email DLP, Insider Risks, ComplianceA Beginner’s Guide to Cybersecurity Frameworks







